What do the Super Bowl and cybersecurity have in common?
To win the big games, teams need both offense and defense. On Jan. 31, the U.S. Government did just that when they disrupted the KV Botnet used by China-sponsored Volt Typhoon.
For far too long, cybersecurity has been considered “preventive” or “reactive.” The industry was developed around defending and protecting assets. The concept of active defense gained interest, but it was misinterpreted and thought of instead as hacking back.
The National Institute of Standards and Technology (NIST) has defined active cyber defense as "synchronized, real-time capability to discover, detect, analyze, and mitigate threats and vulnerabilities." Active defense still means playing defense.
So, how do we go on offense? As an industry, our approach has become littered with legal pitfalls, significant risks and a lack of ongoing capability. Military organizations are uniquely designed to create and sustain long-term offensive cyberspace operations. As sexy and enticing as that sounds, it's restricted to operations against foreign adversaries and nation-states as a matter of law. But that’s not the only option we have for a good offense.
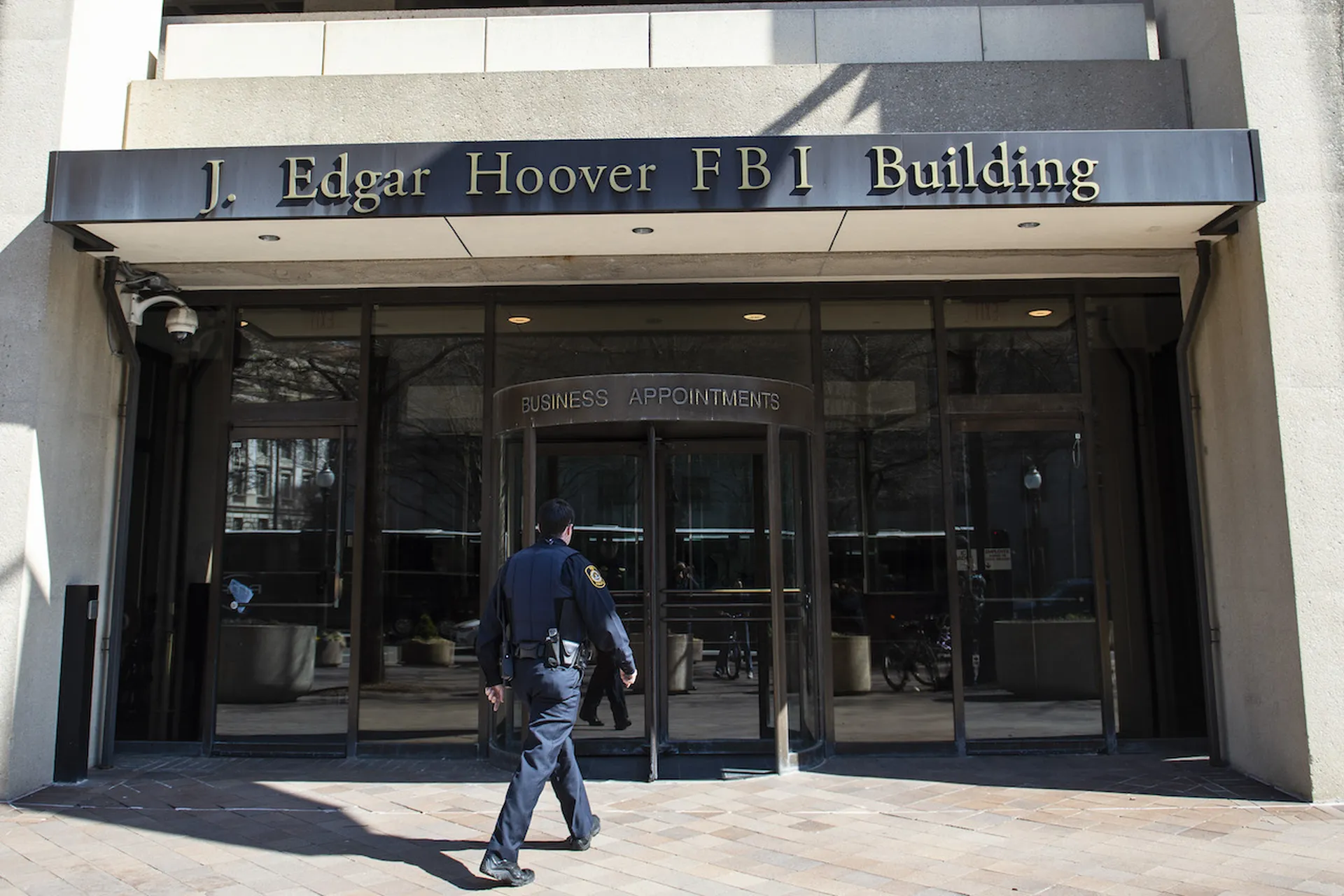
Enter the FBI
The FBI operates as the primary federal investigative organization tasked with responding to cyberattacks and intrusions. We are now witnessing the rise of offensive cyber operations by a domestic law enforcement agency that has demonstrated a significant ability to identify, penetrate, and dismantle criminal and nation-state networks. What once was an anomaly has matured to become a standard part of the investigative arsenal available to actively engage and disrupt transnational criminal groups and nation-state actors.
In November 2022, I had the opportunity to participate in a panel discussion with the FBI Supervisory Special Agent, who led the investigation into the takedown of the Hive ransomware group. What was striking for me was how far the FBI had come since the days 23 years prior when I spent a year conducting in-service training for their Computer Analysis Response Team: CART. The student had become the master.
The dismantling of Hive was directed at a transnational criminal group, a collection of criminals motivated by financial greed. Although the cybercriminals were technically savvy, we had finally reached an inflection point in cyberspace where law enforcement was at least on par with their adversary, if not more adept.
But that was a criminal group. The more significant challenge confronting the FBI was moving beyond investigation and addressing the nation-state threat. Naming and shaming could only do so much, which rarely resulted in a behavior change in the targeted adversary. The odds of winning PowerBall were better than the chance of an indicted foreign intelligence officer seeing the inside of a U.S. courtroom.
A logical move was to target the infrastructure that underpinned the cyber capability to deny our adversaries the cyberspace assets needed to conduct their campaigns.
Enter Volt Typhoon, the state-sponsored threat actor from China.
Volt Typhoon’s targets defied traditional espionage. According to a recent joint CISA/FBI/NSA advisory issued February 7: "Volt Typhoon's choice of targets and pattern of behavior is not consistent with traditional cyber espionage or intelligence gathering operations, and the U.S. authoring agencies assess with high confidence that Volt Typhoon actors are pre-positioning themselves on IT networks to enable lateral movement to OT assets to disrupt functions."
It's clear what Volt Typhoon intends. They are preparing for a future war. In a column for SC Media in December 2023, I noted that this was Intelligence Preparation of the Battlefield.
We can’t allow China to operate unchecked. In conventional warfare, destroying the enemy's ability to wage war is the main objective to achieve lasting peace. Naming and shaming and serving up a multitude of indictments would ring hollow. China would do what they've always done: deflect blame and accuse the United States of being the aggressor in cyberspace.
It was time to go on offense and enact more preventative measures. With the assistance of "numerous private-sector entities," the FBI launched an offensive campaign against the KV Botnet.
Notably, this head-to-head battle wasn't against a traditional criminal group. It was against a top-tier nation-state threat actor with deep technical expertise and even deeper pockets. China would have a nearly overwhelming capability to resource an offensive cyber campaign. This battle was David versus Goliath, and Goliath had more people on cyber than the FBI had in total special agents. The total number of FBI agents assigned to cyber is classified, according to the 2023 budget request.
In the book Emerging Cyber Threats and Cognitive Vulnerabilities, the authors estimated in 2017 that China had more people actively involved in cyber than the United States, United Kingdom, Russia, Germany, and North Korea combined.
So we can't expect China and Volt Typhoon to give up that easily. Winning the war is one thing; winning the peace is a more difficult job. The KV Botnet was dismantled, but could we keep it offline and deny China the ability to reconstitute its operations?
Yes.
We have entered a new phase in a modern digital war. During World War II, G-Men looked for German and Japanese agents and diligently worked to protect our borders from the enemy. America never expected the FBI to field soldiers and repel an invasion – that was the military's job.
In 2024, the FBI is fighting in cyberspace the same enemy our military may one day engage on the battlefield.
For now, score one for David.
Morgan Wright, chief security advisor, SentinelOne