Water utilities stand at the forefront of critical infrastructure, yet they face unprecedented vulnerabilities in cybersecurity. Unlike many other organizations in different verticals, although they might suffer financially if hit by a cyberattack, the impact on water utilities in the event of a successful attack could jeopardize a critical resource for human well-being: water.
For instance, in a 2021 attack on a Florida water plant, hackers attempted to increase sodium hydroxide in the water supply to 100 times higher than usual. If successful, this attack could have resulted in thousands of people being poisoned. Since then, cyber-attacks on water utilities have increased tremendously. Earlier this year, the Municipal Water Authority of Aliquippa in Pennsylvania confirmed that hackers took control of a booster station, although fortunately, the drinking water remained safe. Another successful attack targeted an Irish utility, disrupting the water supply for two days.
Water utilities are vulnerable because they rely on operational technology (OT) systems and industrial control systems (ICS), which control critical processes such as water treatment and distribution. The increased digitization and connectivity of these systems have expanded the attack surface, making them prime targets for threat actors. Weak or default credentials, remote service technologies, and communication protocol vulnerabilities are entry points for attackers, who exploit the interconnectedness between IT and OT environments to infiltrate systems directly and deploy ransomware.
Finally, water utilities often grapple with limited IT staff and budget constraints, hindering their ability to implement robust cybersecurity measures. The combination of resource constraints and legacy systems creates a perfect storm, placing the water sector in a precarious position. The prevalence of legacy systems where multiple old vulnerabilities reside makes the water sector especially vulnerable to cyber-attacks.
Patching challenges
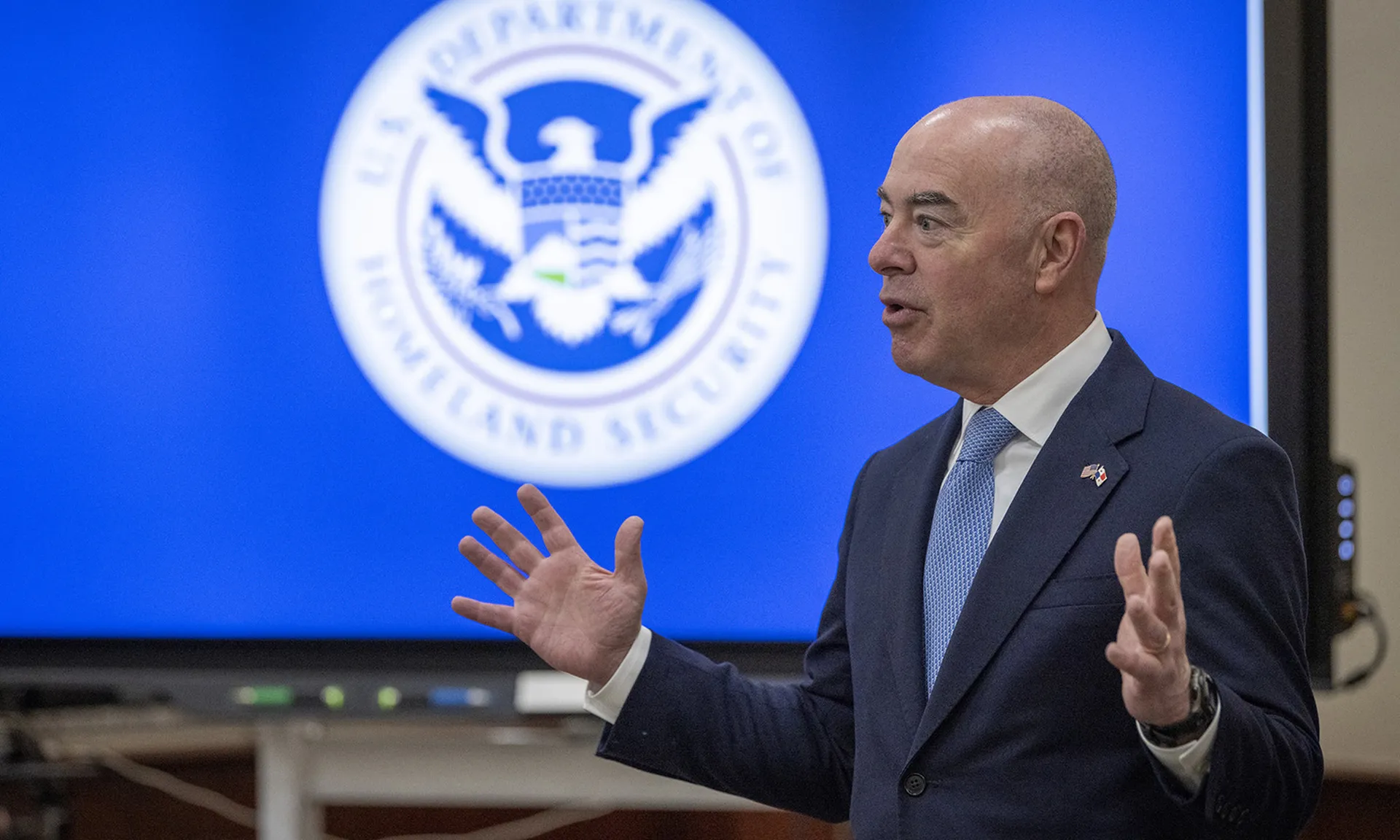
CISA recently took an important step to improve the security of water utilities by introducing a free vulnerability scanning service in September last year. While this will undoubtedly enhance the situation by aiding water utilities in identifying vulnerabilities under limited resources, it does not assist in remediating vulnerabilities, which teams can address by applying compensating controls or patches.
Patching vulnerabilities has become incredibly challenging for water utilities. First, utilities often have a large and geographically dispersed infrastructure, making managing updates across multiple locations difficult. They also operate in complex environments with diverse OT and IT systems that may have different patching requirements. Additionally, they may have poor asset discovery mechanisms and processes, which can lead to a lack of health monitoring. Further, utilities prioritize operational uptime, making scheduling downtime for patch deployment difficult. And finally, utilities may have legacy systems, which are hard to patch yet are still often critical to the facility's operation, meaning the utility cannot simply eliminate their usage. This complexity can make it challenging to implement a comprehensive security strategy.
How utilities can foster cyber resilience
Addressing cybersecurity challenges in the water sector requires collaborative efforts between public and private entities. Sharing threat intelligence, best practices, and experienced personnel can bolster defenses against cyber threats.
Moreover, coordinated efforts within utility organizations are essential to ensure systematic patching and efficient cybersecurity practices across departments and facilities. Water utilities must implement a centralized patch management system that lets utilities deploy patches across all sites from a single interface remotely.
This system should support automated patch deployment, scheduling, and reporting to streamline patching and ensure consistency across diverse OT and IT systems. It should also let utilities implement a risk-based approach to prioritize patching based on the criticality of assets and the severity of vulnerabilities. We recommend utilities conduct regular risk assessments to identify high-risk systems and vulnerabilities that require immediate attention, ensuring that resources are allocated effectively to mitigate the most significant risks first and that they can manage the entire process from a single interface. Otherwise, it’s more complex, and there are higher chances that vulnerabilities go unnoticed.
Finally, utilities must implement compensating controls or temporary workarounds for vulnerabilities that teams cannot immediately patch, especially in the case of critical systems or legacy infrastructure. These controls may include network segmentation, intrusion detection systems, or enhanced monitoring to mitigate the risk of exploitation until patches are applied.
Drinking water systems are an essential community lifeline. While the government must put significant efforts into protecting water systems from cyberattacks, cybersecurity software vendors could do more to contribute to this vital task – for example, by offering increased discounts or even free services for the water sector. Together, we can build a more secure and resilient future for our water infrastructure, mitigate the risks posed by legacy vulnerabilities, and safeguard critical resources.
Mike Walters, co-founder and president, Action1