It’s been nearly 20 years since the Open Web Application Security Project (OWASP) was launched. Today, OWASP’s Top 10 is the de facto generic vulnerability standard for many in the industry, with valuable insights into where we are as an industry and where we continue to struggle.
In 2021, the top 10 got its first major update since 2017. Many of the same problems remain, while new ones have been added. Security practitioners have been working to unpack and apply the lessons in the last 12 months.
One of the more valuable tools has been an Immersive Labs eBook that serves as a cheat sheet and delves deep into the meaning behind each item on the revised list .
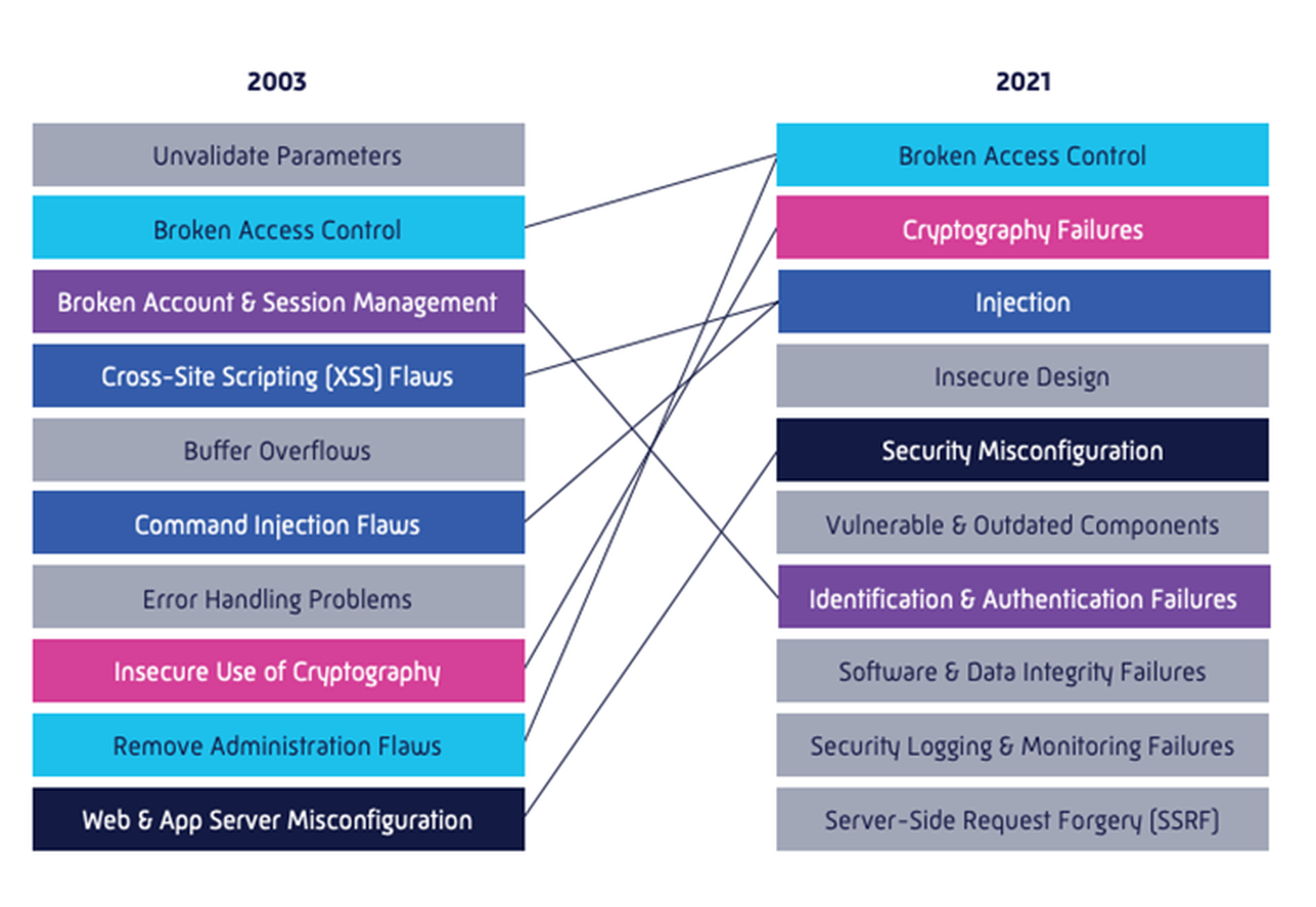
One visual from the eBook highlights what has changed since the first OWASP Top 10 was released in 2003:
Changes since 2017
The report also focuses on what has changed since 2017. In a related blog post on the subject, Immersive Labs Principal Application Security Engineer Sean Wright noted that every single item from 2017 is still on the current list, either directly or combined in a new category.
“If we were to take the more optimistic view, the fact that these individual categories have now been grouped together could mean that they are less prevalent than before,” Wright wrote, while also noting the introduction of a new term for 2021: “failures.”
“This represents a shift in the nature of the most prevalent vulnerabilities,” he continued. “In the past, many vulnerabilities were introduced via some type of logical or functional flaw, typically an issue with the code itself. Now, however, we’re seeing security baked into things such as frameworks and services. To me, the term ‘failures’ recognizes this, and reframes the problem as either the failure to use, or the misuse of, security features and configurations.”
The updated list also marks the first time “Insecure Design” has appeared on the list, notable simply because it relates to a missing (or flawed) step before development even begins.
“This is a really important step towards ‘shifting left’ as design is one of the elements that sits to the left of an application’s development lifecycle,” Wright added.
20 years of lessons
Wright’s post also includes a visual showing each Top 10 list from previous years, and his commentary on the main lessons of the last two decades:
“Alarmingly, if we review all eight lists side-by-side, we will see the following categories appearing in all of them (either as the same category or grouped into another category):
- Broken Access Control
- Broken Account and Session Management (now referred to as Identification and Authentication Failures)
- Injection
- Sensitive Data Exposure (now referred to as Cryptographic Failures)
- Security Misconfiguration
That means 18 years is still not long enough for us, as an industry, to remedy these flaws. With the exception of the Injection category, which is quite broad, the other four are business logic or misuse flaws. If we compare the first list from 2003 with this year’s list, we can see that seven of the 10 items are still an issue in some shape or form.
All of this means we have to change our approach – and I think we are, albeit slowly. The best thing we can do now is to focus on empowering the people who build, test, and secure these applications.”




