(A preview of the upcoming SC Media eBook “Launching MDR: How to configure, deploy and optimize”)
Now that you’ve configured and deployed MDR, it won’t take long to see the pay-off. With a pool of dedicated threat hunters and infosec warriors vigilantly attending to your network, your organization can expect to see dramatic improvement when it comes to discovering and eliminating potential threats.
But as threats evolve over time, your MDR service must be able to do the same. Optimizing MDR is critical to staying ahead of threats, as well as developing your organization’s long-term threat hunting ‘muscle’ and incident response capability. Neglecting this opportunity is tantamount to buying a gym membership, and simply sticking to the same machines year after year even as newer machines and specialized training become available. With that approach, you’ll only get what you originally signed up for (even though you could be getting quite a bit more).
So what does optimization look like, and how can organizations work with their MDR provider to maximize the value of this service over time?
How to optimize MDR
In a healthy MDR partnership, the vendor and customer are on the same page when it comes to developing the customer’s threat hunting maturity and independence over time. In this arrangement, the vendor takes on more of a coaching role (as an extension to their threat hunting services) and advises customers how to build up their own SOC operation from within.
#1: Make transparency part of the deal
Configuring and deploying MDR requires the customer to give their provider access to sensitive data and other assets. To optimize the MDR relationship, it can be very beneficial for the provider to reciprocate that transparency by letting the customer get a glimpse into the tech stack and tools powering MDR operations.
Unfortunately, this sort of arrangement doesn’t always pan out. Some MDR providers may wish to keep their tooling a secret, thus leaving the customer perpetually dependent on their specific service. But that shouldn’t be the case, says Greg Rosenberg, Director of Sales Engineering at Sophos.
“It’s important to align with the customer, to give them the opportunity to learn – as much as possible – your tooling and stack. In other words, be transparent as possible with how you detect malicious activity.”
Rosenberg laments that the market doesn’t generally share his team’s philosophy.
“There’s a real lack of transparency I see in the market, which demonstrates itself in the language that we use. Is there really a difference between a threat hunt and investigation? Yes. Are there differences in the types of threat hunts? Yes. Are there differences in the telemetry that providers ingest? Yes. But from an organizational perspective, it's really hard to know the difference, especially if one of the reasons you're buying a service is because you've acknowledged you don't necessarily have the maturity or knowledge.”
Therefore, organizations are encouraged to ask vendors how they conduct MDR ops so that they can learn and begin integrating these practices on their own over time.
#2: Look for guided training and onboarding opportunities
Some MDR providers have begun adding training and onboarding programs as extensions to their regular service. Customers should be on the lookout for such opportunities to give their IT staff hands-on experience and supervised learning from some of the best threat hunters in the business. This may take the form of a guided onboarding platform that gives customers more visibility over the same threat intel and alerts that the vendor uses to perform their service.
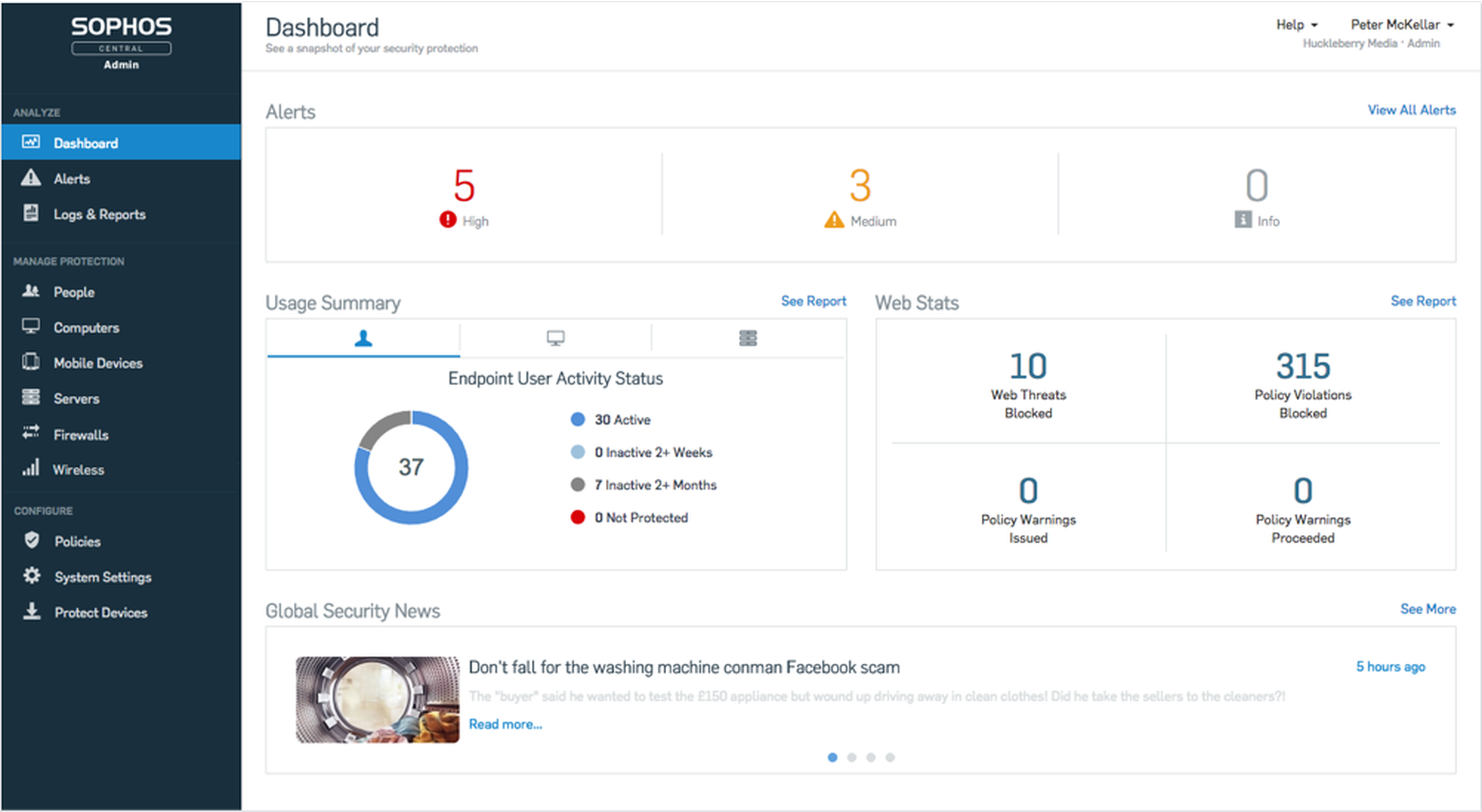
“The methodology and philosophy over time is the most important thing that a [MDR provider] can share with customers because the threats are going to change,” says Rosenberg. “We very much try to include training as part of this, at least on the front end with what we call Sophos Central. It’s a web-based user interface that facilitates a lot of what we ourselves use for discovering and tracking threats. Even though you're buying a managed service, we want you to be able to have hands-on knowledge to facilitate that journey.”
#3: Continue to request demonstrations of value and service evolution
Finally, organizations should continue to work closely with their provider, being receptive to their recommendations while not shying away from asking their provider to demonstrate added value over time.
MDR reports or findings are a great way for customers to see their investment pay off and improve over time. These reports should be shared on a routine basis (such as biweekly or monthly), and provide intel on the latest threats and vulnerabilities, as well as any protective actions the vendor has taken on the customer’s behalf. These reports are good for establishing a clear vocabulary between both parties and giving the customer’s security team more insight into how sophisticated threats are dealt with.
“Organizations should literally be able to pick up the phone and reach out to the vendor’s operations analyst, without restriction. That ability to ask how the service is running and whether there’s been any changes in the environment, that should be baked into your regular course of business,” says Rosenberg.
Conclusion
Optimizing MDR over the long term isn’t guaranteed. Just as the customer can play a crucial role in helping the vendor configure MDR so as to fulfill business objectives, so too can the vendor play an important role in expanding the customer’s security awareness and capacity for eliminating advanced threats. To get the most out of this relationship, it’s incumbent on both parties to be transparent, available and receptive to change along the way.




