A cryptographic vulnerability in the Tonelli Shanks modular algorithm, which is used in popular cryptographic library OpenSSL, can lead to denial-of-service attacks and can “definitely be weaponized” in the current threat environment, according to an NSA official.
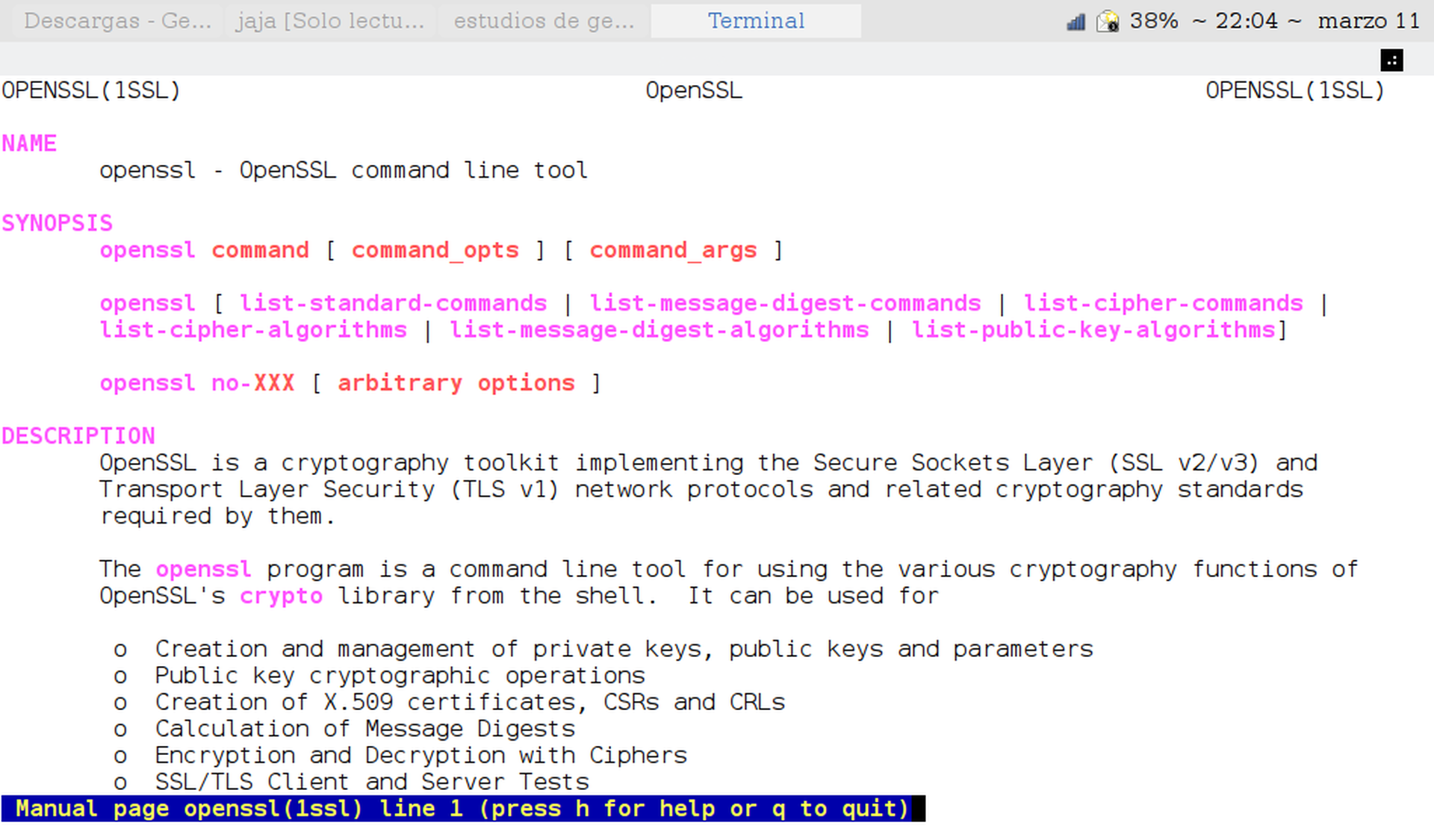
The bug — discovered by two Google employees, security researcher Tavis Ormandy and software engineer David Benjamin, and is being tracked under CVE-2022-0778 — affects the BN_mod_sqrt() function in OpenSSL, which is used to compute the modular square root and parses certificates that use elliptic curve public key encryption.
This process can be exploited if an attacker submits a certificate with broken curve parameters, thus triggering an infinite loop in the program and leading to a denial of service.
“Since certificate parsing happens prior to verification of the certificate signature, any process that parses an externally supplied certificate may thus be subject to a denial of service attack,” OpenSSL said in a March 15 security advisory. “The infinite loop can also be reached when parsing crafted private keys as they can contain explicit elliptic curve parameters.”
The bug can be exploited in TLS clients consuming server certificates, TLS servers consuming client certificates, hosting providers who take certificates or private keys from their customers, authorities that parse certification requests from their subscribers and “anything else that parses ASN.1 elliptic curve parameters." It affects OpenSSL versions 1.02, 1.1.1, and 3.0, all of which have been patched.
OpenSSL is a core component of Unix and Linux-based systems, and is also bundled into software applications that run on Windows. The vulnerability received a shout out from the NSA’s top cybersecurity official, who warned defenders not to be fooled by the (relatively) low severity rating and patch immediately.
“With the current state of internet threats, recommend patching CVE-2022-0778 immediately…This flaw enables a pre-authentication DOS attack on OpenSSL,” Rob Joyce, director of the NSA’s cybersecurity directorate, wrote Monday on Twitter. “I know it is ‘only’ rated a 7.5 [out of 10], but definitely can be weaponized.”
Paul Ducklin, a security researcher at Sophos, noted that it was “ironic” because the vulnerability appears to exploit a glitch in programs or applications that correctly follow otherwise best practices for secure connection, while failing to affect programs and applications that use less secure protocols.
“Amusingly, if we’re allowed to say that, the bug apparently only gets triggered if a program decides to do the right thing when making or accepting a secure connection (e.g. an HTTPS browsing request), and verifies the cryptographic certificate supplied by the other end,” Ducklin wrote on March 18. “A browser (or an updater, or a login portal, or whatever it might be) that simply accepted the cryptographic credentials of the other end, and didn’t bother to check whether some moderately trustworthy authority had issued them in the first place…would, ironically, be unaffected.”
Ducklin noted that the while the bug was less serious than an exploitable vulnerability that could allow an attacker to surreptitiously install malware on victim devices, it was worth paying attention to because it could indicate the presence of additional unknown flaws and bugs in other little known but commonly used software libraries — like Log4J and Heartbleed, another OpenSSL vulnerability — have shown the potential for broad-based impact on users.