
Massive. That’s how researchers at Check Point on Monday described the data and documents reportedly released Sunday by the Vice Society ransomware gang after the Los Angeles Unified School District refused to pay a ransom following the group’s attack on LAUSD in September.
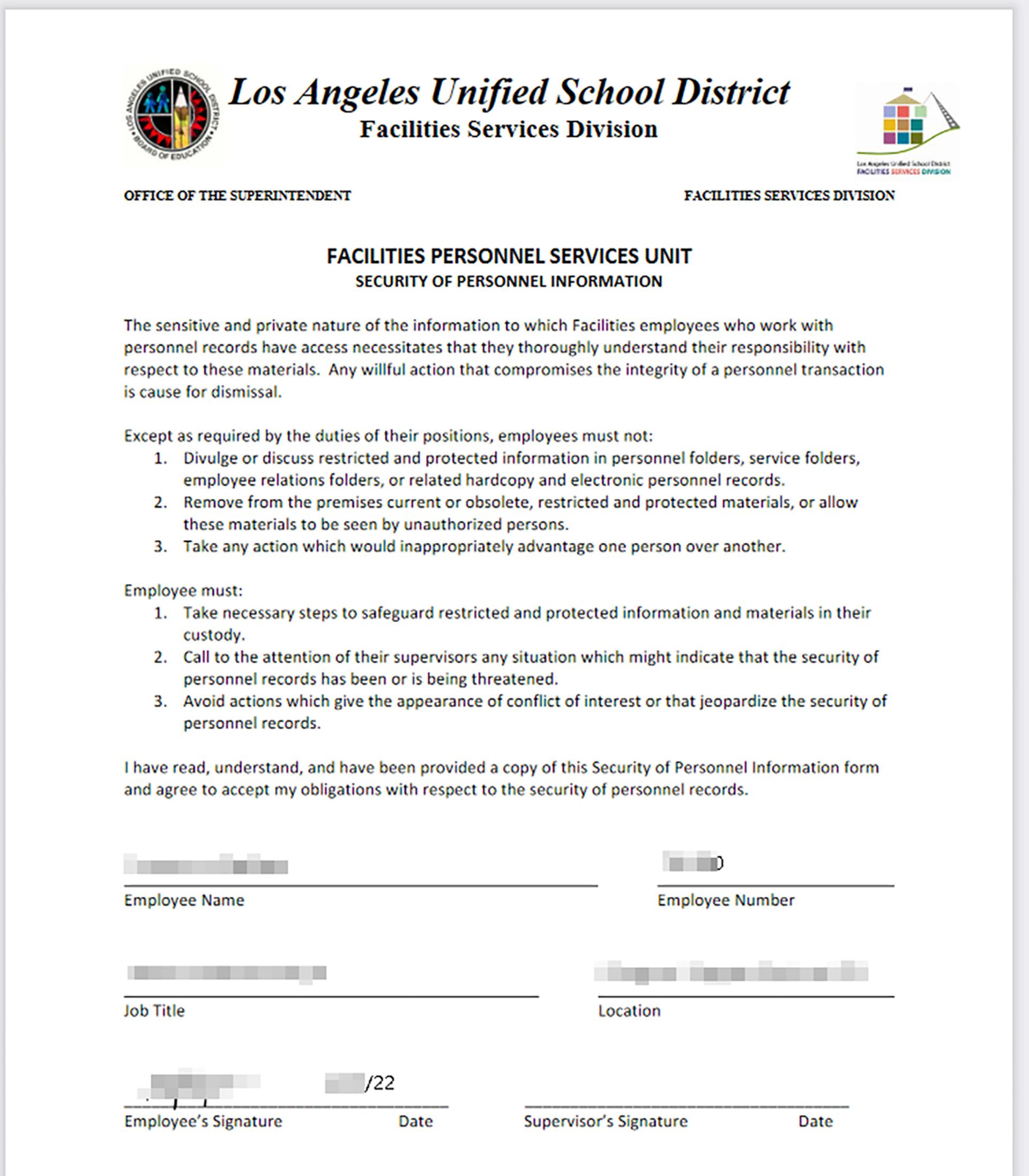
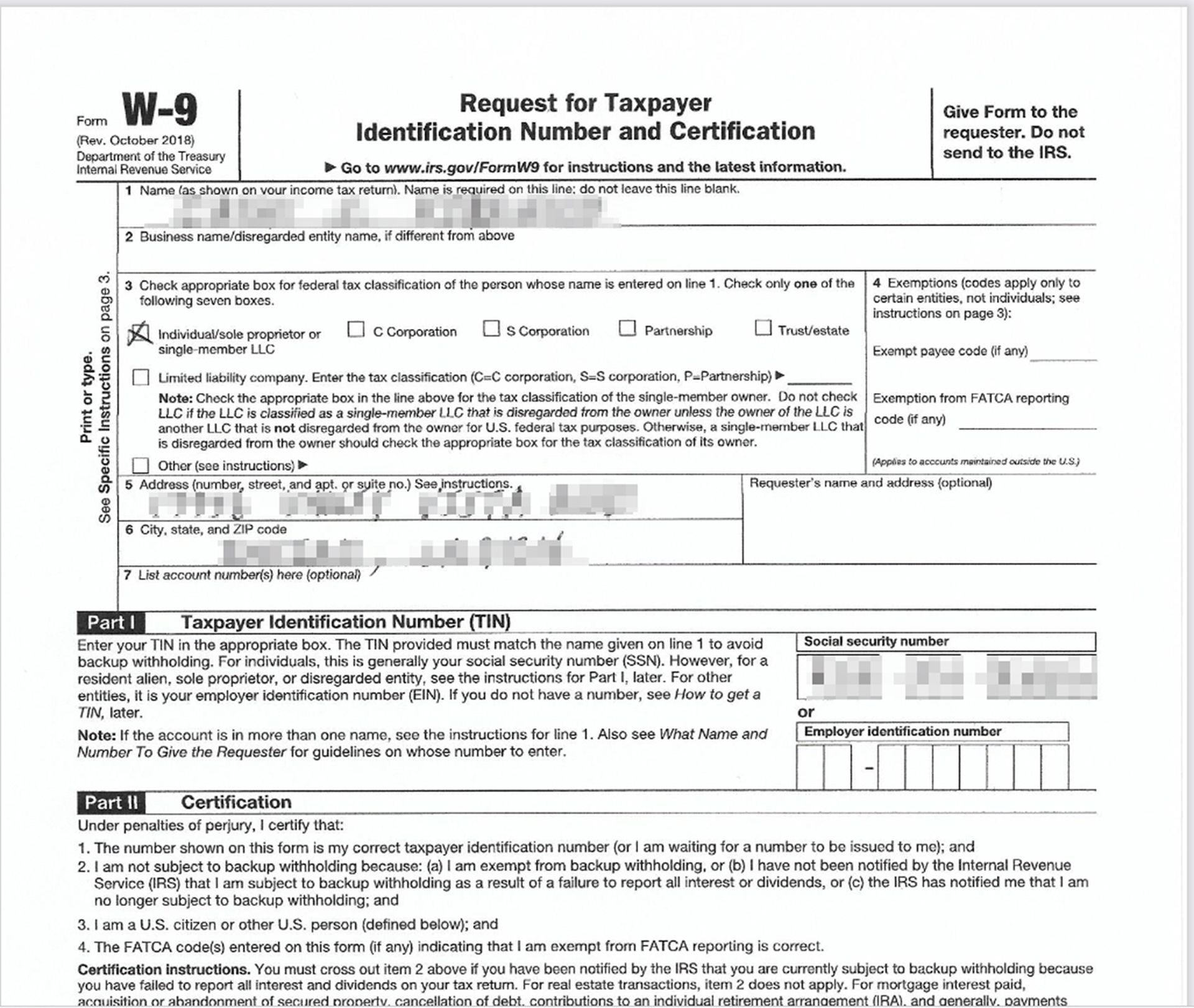
"We had our researchers look into it overnight,” said Liad Mizrachi, a security researcher at Check Point Software. “Our researchers managed to track the hackers' platform on the dark net and see what they leaked. In short, it’s over 248,000 files of different kinds of data. We’re seeing SSNs, contracts, invoices, passports, and more.”
Mizrachi added that it’s important to stress there’s a bigger trend here: The education sector has experienced a significant rise in cyberattacks. In September alone, Mizrachi said an American education organization was under a weekly average of more than 740 attacks per week — a 37% increase year-over-year. Also, when it comes to ransomware, Mizrachi said Check Point data showed that 1 out of 98 organizations in the United States gets attacked by ransomware every week — a 15% increase from last September.
LAUSD Superintendent Alberto Carvalho made the district’s position clear in a Tweet on Monday, when he said: “I understand there will be many opinions on this matter but, simply said, negotiating with cybercriminals attempting to extort education dollars from our kids, teachers, and staff will never be a justifiable option. LAUSD refuses to pay ransom.”
Den Jones, CSO at Banyan Security, said the general rule is that most professionals — law enforcement included — will recommend not to pay any ransom when infected with ransomware. Jones said the LAUSD is correct in following this protocol, and for having reported the breach to the U.S. government. Jones added when organizations report to federal agencies such as CISA, the FBI or the U.S. Secret Service, other agencies are also notified.
“When organizations give in to hackers and pay ransoms, they are actively providing an incentive for attackers to continue their destructive activities while simultaneously using this influx of funds to ‘improve’ the efficacy of their hacks,” Jones said. “If an organization is the victim of a ransomware attack, companies that specialize in mitigating ransomware attacks, even as they are under way, should be contacted. These organizations have the experience and knowledge to communicate with the hackers to hopefully come to a resolution that does not include the payout of a ransom. While that’s happening, IT and security teams must work together to ensure critical areas of the network are segmented to minimize damage.”
Ilia Kolochenko, founder of ImmuniWeb, and a member of Europol Data Protection Experts Network, added that we should expect a further surge of ransomware campaigns that are relatively simple to run, are hardly investigable by law enforcement agencies, and bring huge profits, being a perfect “business” compared with other cyberattacks.
“With the new extortion tactics, not just the breached companies are blackmailed — but all the individuals whose contact details are available within the stolen data,” Kolochenko said. “So, if your personal data is stolen, you can pay hundreds of dollars to prevent its publication if the breached company eventually refuses to pay the ransom. Sadly, victims are oftentimes under-compensated.”
Casey Ellis, founder and CTO at Bugcrowd, said the FBI bases its advice on not encouraging victims to provide perpetrators with proceeds of a crime, which is “technically correct” advice from a law enforcement agency and makes sense as a good starting point — plus, it's ethically the right thing to do. In reality, Ellis said a victim must make an economically rational decision about whether the cost of paying a ransom and restoring business is less than the cost of losing business and/or recovering from the attack.
“The challenge with today’s ransomware operators is that their ability to pick and tailor a ransom that does not leave money on the table, but is also not high enough to drive a victim not to pay, is quite sophisticated at this point,” Ellis said. “In the case of LAUSD, I applaud the department’s moral and ethical stance, but it’s important to note that this decision will still incur costs in the form of data leakage and cleanup, making it difficult to determine it as ‘the best approach.’ Decisions like this have equities that vary wildly from case to case.”



