We are at a crucial juncture in phishing defense. The impact of the COVID-19 pandemic made it clear that organizations were unprepared for a worldwide data security crisis. Companies were forced into digital transformations and employees were required to operate remotely.
This unanticipated disruption to operations put extensive pressure on security teams while companies focused on business continuity rather than security compliance. Organizations were forced to adapt to new and more sophisticated phishing attacks. Many companies that were unable to adapt and defend against the quickly evolving attack vectors and tactics learned the hard way that basic security defenses were inadequate.
That pain was captured in a study CyberRisk Alliance Business Intelligence conducted in early 2021 and again in late 2021 among more than 300 IT and cybersecurity decision makers and practitioners from large organizations across North America, Europe, the Middle East, and the Asia/Pacific region. Among the study’s key findings:
- In Q3, ransomware remained the top phishing incident, experienced by half of all respondents.
- The average number of phishing incidents for those that experienced one in Q3 2021 was 5 (the same as in Q1 2021).
- Phishing represented an average of 29% of all cybersecurity incidents in Q3 (compared to 32% in Q1).
- Nearly half of respondents experienced an increase in phishing in Q3 (significantly lower than Q1); and about one in four experienced the same frequency of phishing since Q1.
- Email attachments and links were the top sources for phishing, accounting for about one third of all phishing incidents (slightly more compared to Q1).
- Financial loss remains the top impact of phishing incidents.
Sophos study: Phishing means different things to different people
The challenges unleashed by phishing attacks is further illustrated in a survey Sophos commissioned (also in 2021) among 5,400 IT professionals at the IT frontline around the globe.
As you’ll see, the research uncovers many of the same challenges we saw in the CyberRisk Alliance study.
One of the findings from the Sophos survey is that even among IT professionals there is wide variation in what people consider to be a phishing attack. The most common understanding is emails that falsely claim to be from a legitimate organization, usually combined with a threat or request for information. While this was the most popular answer, fewer than six in ten (57%) respondents selected this option, illustrating the breadth of meanings understood by phishing.
46% of respondents consider Business Email Compromise (BEC) attacks to be phishing, while over a third (36%) understand phishing to include threadjacking i.e. when attackers insert themselves into a legitimate email thread as part of an attack.
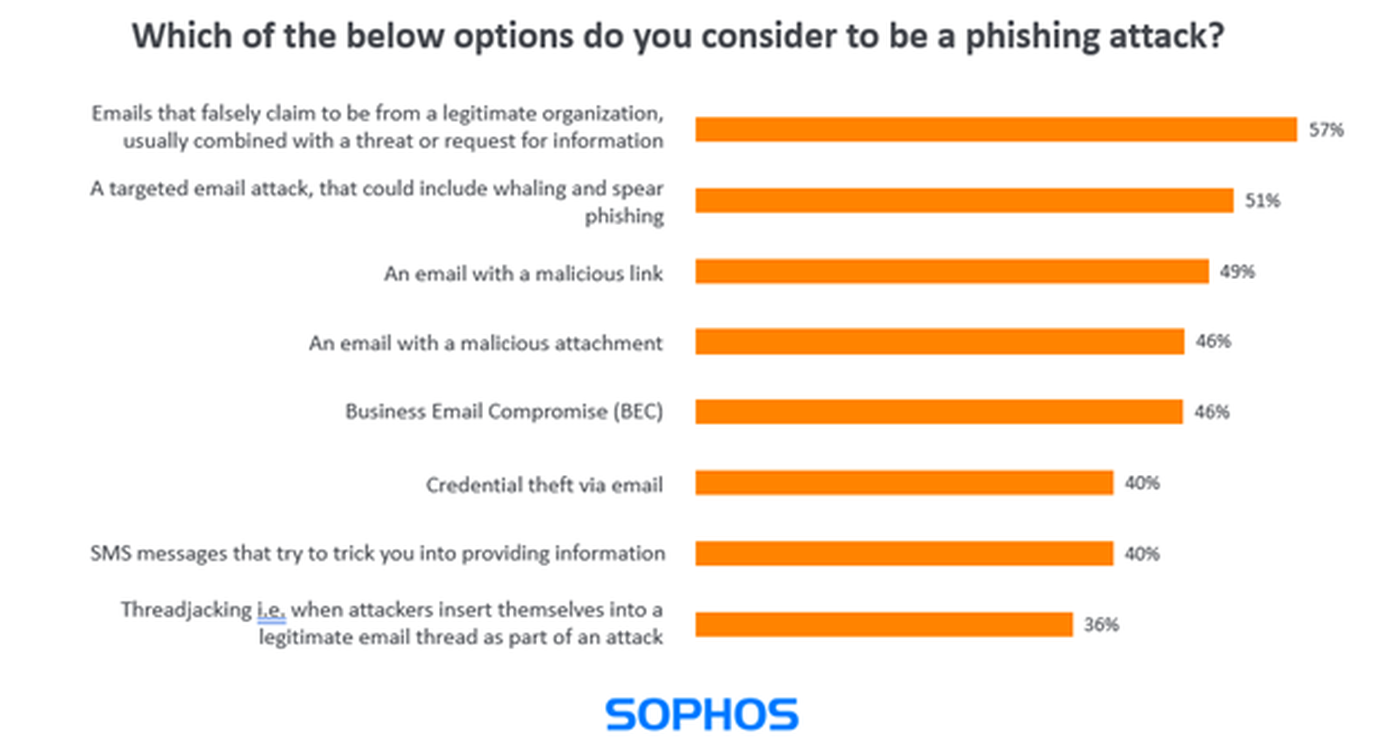
With this extensive variation in understanding of phishing attacks among IT professionals, it’s reasonable to expect a similar or greater range of interpretations among non-IT employees.
This is a useful reminder to be mindful of the different interpretations of the word ‘phishing’ when providing educational resources and user awareness training. Without the correct context, the training will be less effective.
Phishing has increased since the pandemic
Like the CyberRisk Alliance study, Sophos’ research captures the challenges organizations have faced amid the pandemic shift to remote operations.
For example, 70% of survey respondents reported an increase in phishing attacks on their organization since the start of the pandemic. All sectors were affected, with central government experiencing the highest increase (77%), closely followed by business and professional services (76%) and healthcare (73%).
Fortunately, 98% of organizations had their phishing awareness program in place before COVID-19 hit. Thanks to these programs, employees will have been well placed to withstand the barrage of phishing emails over the last year.
While this is good news, it’s also a reminder to regularly review and update phishing awareness materials and activities to keep them fresh and relevant.
Read the full report
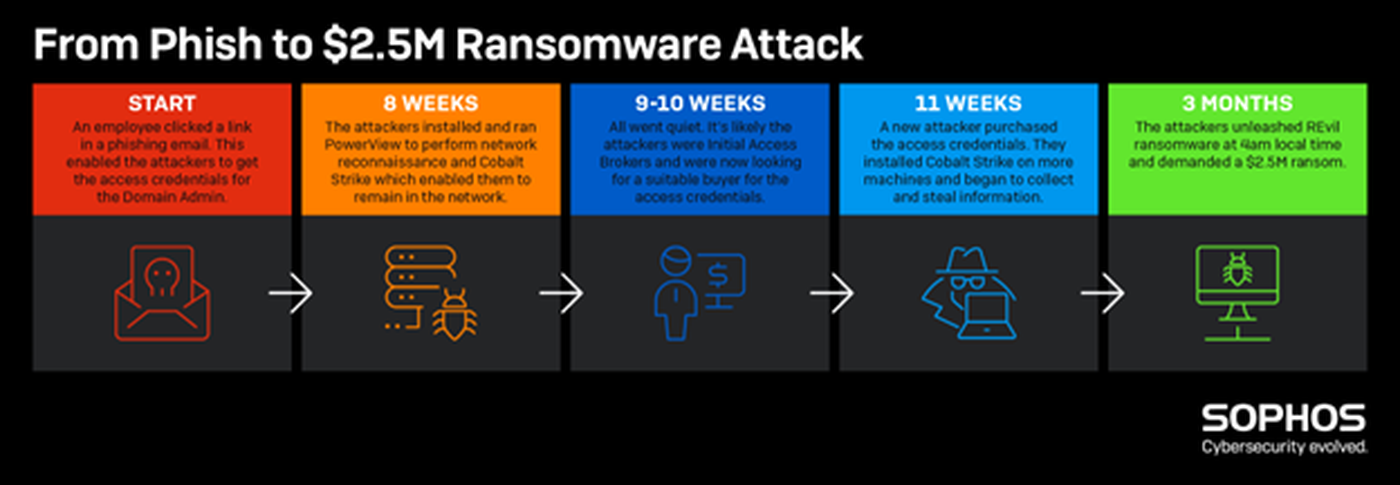
Download the full Sophos Phishing Insights 2021 report to dive deeper into the state of phishing and cybersecurity user education, and the timeline of this attack.




