Researchers from Intel 471 on Thursday reported that ransomware groups are increasingly becoming impacted by disgruntled affiliates, a trend that may cause serious issues for both law enforcement agencies and security teams.
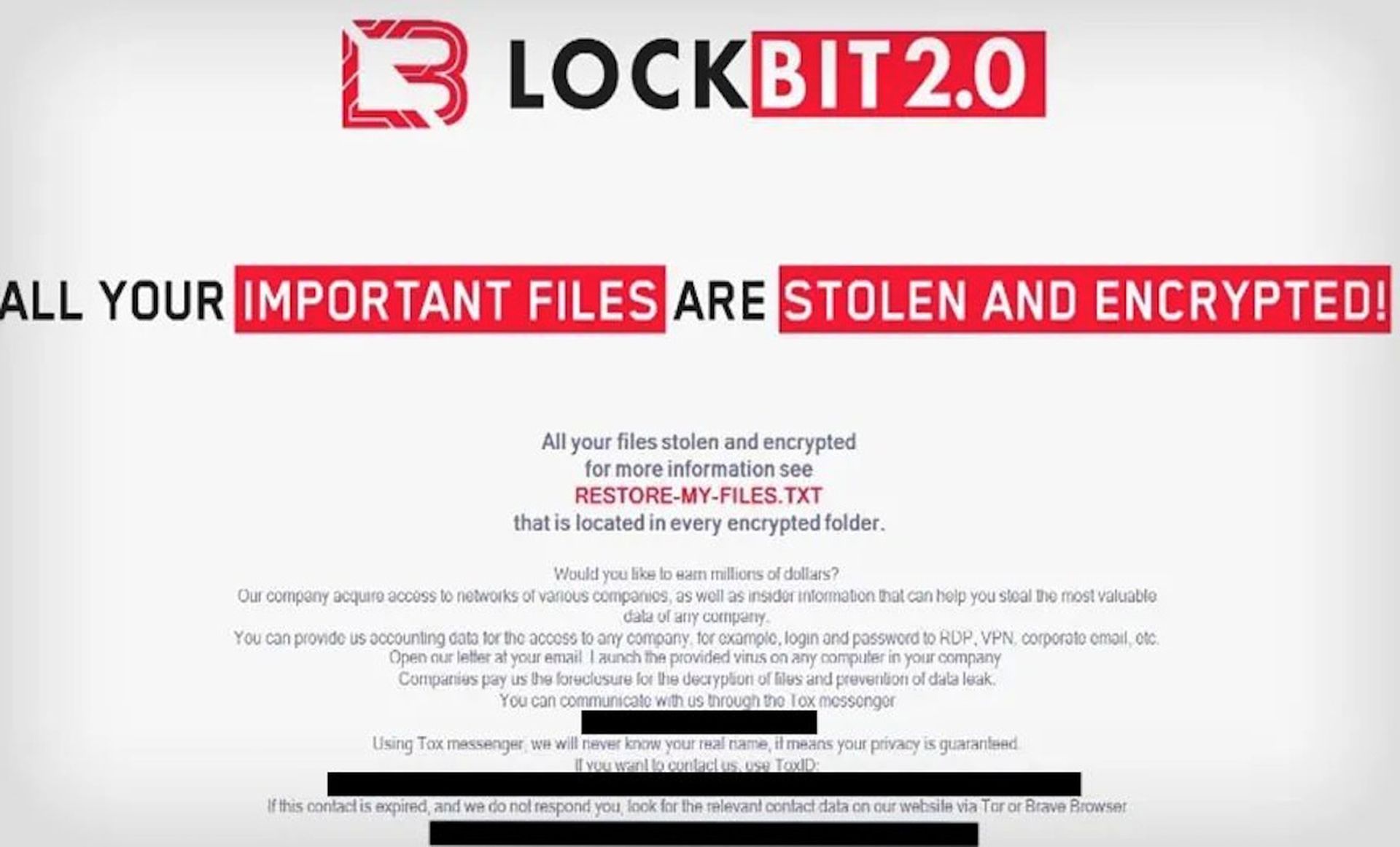
Beth Allen, senior threat intelligence analyst at Intel 471, said a case in point was this past quarter when LockBit files containing builder code were leaked by a disgruntled coder, an action she said demonstrates that even well-established affiliate groups can struggle with operational security.
“This trend is likely to continue in the future as more affiliates become disgruntled,” Allen said. “It will likely create a power vacuum within the cyber underground, spawning an overabundance of new ransomware variants and groups, making it more difficult for law enforcement agencies to track and thwart them, and businesses to defend against them, due to alternate tactics, techniques and procedures (TTPs) used.”
Allen added that ransomware groups are almost certain to continue evolving and adapting their TTPs, along with using well-established ones, such as utilizing double extortion tactics. “The end goal of any ransomware group is to make as much money as possible in the shortest amount of time, while inflicting as much disruption as possible to achieve this,” Allen said.
While Intel 471 observed 455 ransomware attacks in Q3 of this year, a decrease of 72 attacks from Q2, Allen pointed out that overall, the number of businesses impacted by ransomware will likely increase because it’s seen as a highly lucrative business model.
“So with economic instability being predicted globally, individuals will possibly turn to criminal means conducted from the comfort of their own home as a way to supplement their income,” Allen said.
Mike Parkin, senior technical engineer at Vulcan Cyber, added that while an apparent reduction in ransomware attacks is welcome, it doesn’t mean we’re “winning the war,” against these cybercriminal gangs. Parkin said the frequency of these attacks ebb and flow based on everything from law enforcement activity to what exploits are effective to internal politics within, or between, the gangs.
“It’s entirely possible that the advantage currently lies with the defense, at least for now, however, it’s not something we can count on,” Parkin explained. “It’s impossible to predict when the next wave of cybercrime will come rolling in, but we know that it will.”



