As 2022 closed, rail and locomotive rail company Wabtec disclosed that hackers had breached its computer networks earlier in the year and stole sensitive data.
In a public release, the company said the hack took place on March 15, 2022 and the company discovered it on June 26, when they promptly notified the FBI. A subsequent investigation confirmed that certain data was taken from the Wabtec computer environment on June 26.
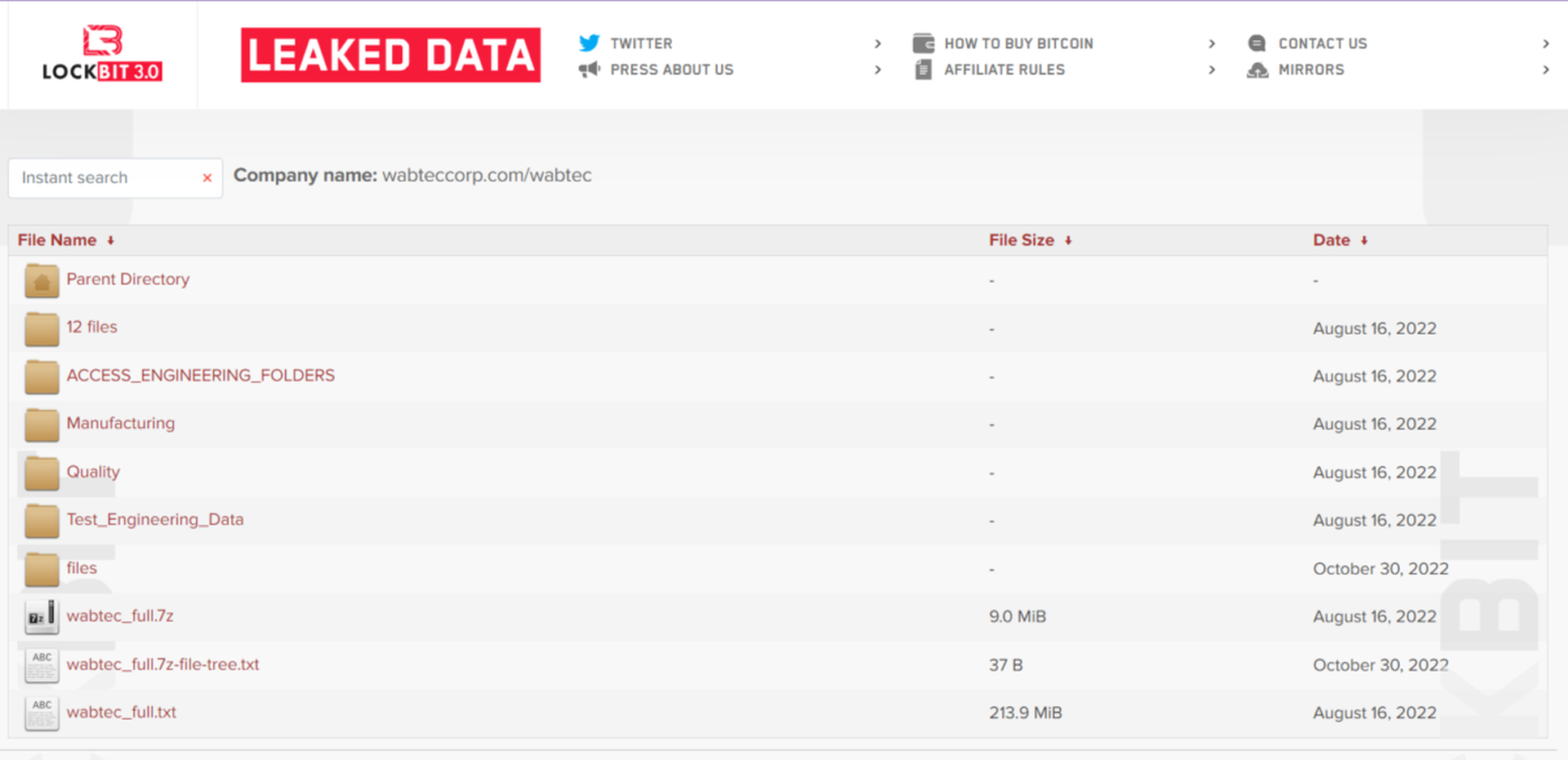
According to local news outlets, sources at one of Wabtec's plants said that it was a ransomware attack, but the company did not officially respond to the rumors. Weeks later, the ransomware group LockBit published samples of data they claimed to have stolen from Wabtec and eventually leaked all stolen data on August 20th, 2022, presumably after the ransom was not paid.
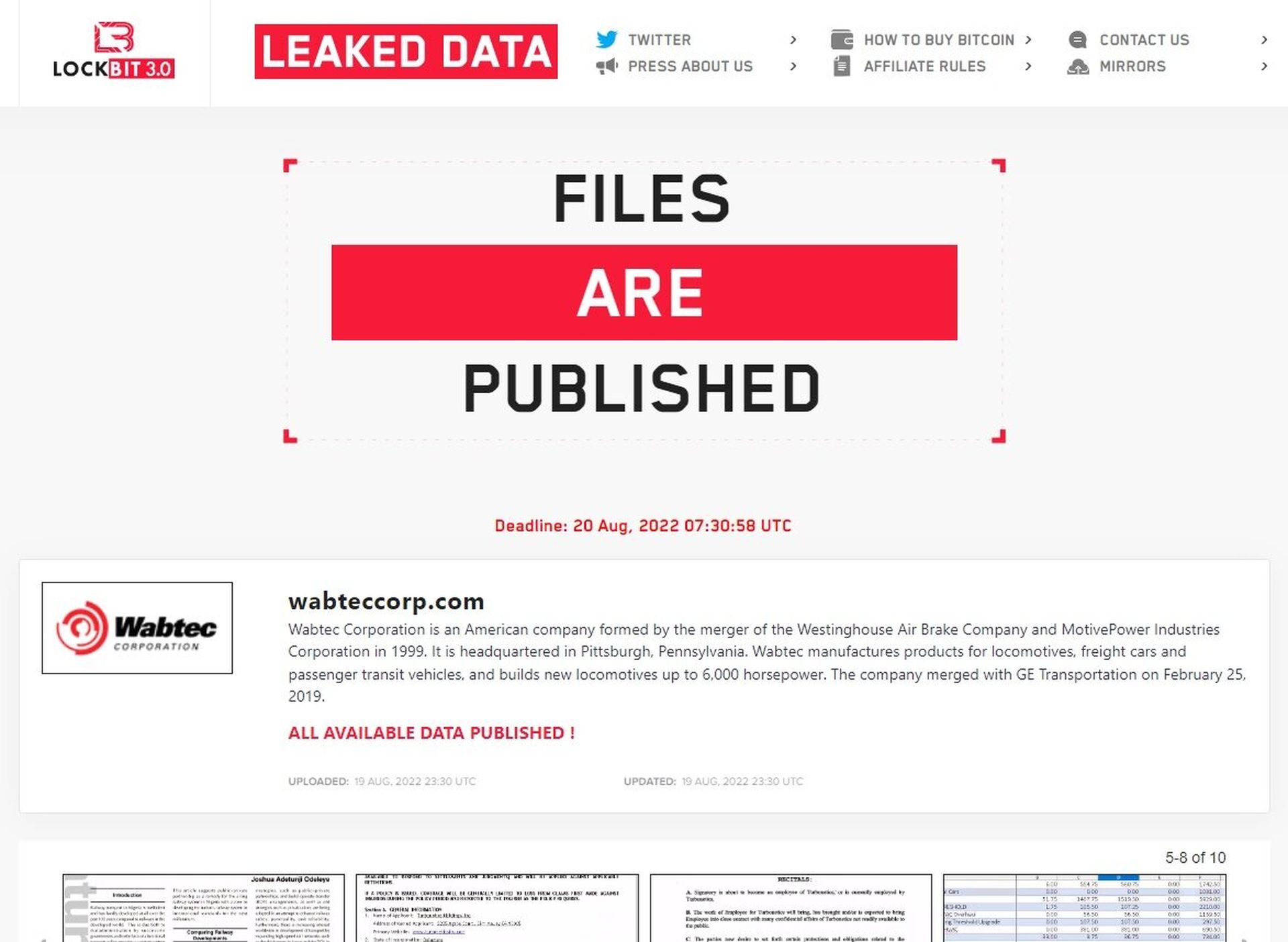
That sample included first and last names, dates of birth, medical records, insurance information, salaries, U.S. Social Security numbers, financial account information, payment card information, criminal convictions or offenses, and sexual orientation/life, religious beliefs and union affiliation.
Wabtec's release does not make it clear whether the stolen data belonged to employees, customers or other parties. SC Media has reached out to the company to get further clarification.
Ron Fabela, co-founder and CTO at SynSaber, said the attack appears to be a straightforward double-extortion attack with the sensitive files published back in August 2022. The data posted on LockBit's disclosure site, identified as belonging to Wabtec, appears to be a combination of internal employee PII, partner/customer invoices, and non-employee PII data.
“What's intriguing is that although the files were published back in August, Wabtec is just now reporting the data lost,” Fabela said. “This lag in breach reporting is not uncommon and continues to be a focus for industry and government policy makers."
Fabela added that while the fact that Wabtec is a a freight rail company garners some interest, there's no evidence anything specific to the industrial control systems, plant operations, or other non-HR data was affected by this attack.
“While industrial processes are not the intended target, widespread IT outages can have a splash damage effect on processes,” he said.
Andrew Hay, chief operating officer at LARES Consulting, pointed out that the discovery of malware more than four months after suspicious activity may indicate a deficiency in the organization's security visibility and response capabilities, but reiterated Fabela's point that such gaps between an incident and notification are common.
“Once the FBI gets involved, it's normal for public disclosure to lag,” said Hay. “Like any criminal case, law enforcement wants to investigate. This is not always a fast process and could take weeks, if not months, to draw accurate conclusions, ascribe attribution, and, where possible, press charges.”
Piyush Pandey, chief executive officer at Pathlock, said truly effective data security isn’t possible without dynamic controls. In the past, Pandey said to properly secure the data within critical business applications, app security teams either had to implement inflexible controls or silo applications entirely, which would often reduce employees' productivity.
“Many organizations are now moving to dynamically mask and anonymize data at the field level and at the point of access, allowing you to easily enforce data governance policies beyond simple role-based controls,” Pandey said. “As for the lag in the notification of the breach, if the majority of data was unencrypted or masked, it could take some time to identify which systems were exposed and how deeply the data was accessed.”



