Researchers at Palo Alto Networks say they have identified another campaign that has been leveraging a remote code execution vulnerability in a popular Zoho password manager and single sign-on service.
The campaign dates back to at least Sept. 17, when the group was observed scanning hundreds of organizations that had yet to install a Sept. 6 update to fix the flaw, including 350 Zoho servers in the U.S. alone. Five days later, they began setting up web shells and exploiting targets across multiple different sectors through October.
“During that window, the actor successfully compromised at least nine global entities across the technology, defense, healthcare, energy and education industries,” wrote researchers Robert Falcone, Jeff White and Peter Renals.
Palo Alto Networks has not formally attributed the campaign to a state or hacking group, but do note substantial overlap in tooling and tactics between this actor and other Chinese hacking groups, most notably APT27, a cyberespionage group linked to China.
Those overlaps include the use of ChinaChopper malware to gain initial access, the use of two tools – Godzilla to set up web shells and a backdoor called NGLite. Both were developed with Chinese instructions, but as the researchers note, they’re also freely available for download of the web. The specific order and methods used during exfiltration also mirrors past APT27 operations.
In September, CISA, the FBI and the U.S. Coast Guard warned that one or multiple state-aligned hacking groups were “likely” exploiting a remote code execution vulnerability in multiple versions of ManageEngine ADSelfService Plus.
The agencies also warned that they had observed it being used against a wide variety of sectors and industries, including “critical infrastructure companies, U.S.-cleared defense contractors, academic institutions, and other entities.” They used the flaw to steal credentials, conduct lateral movement and exfiltrate valuable data from services like Active Directory.
“APT cyber actors have targeted academic institutions, defense contractors, and critical infrastructure entities in multiple industry sectors—including transportation, IT, manufacturing, communications, logistics, and finance. Illicitly obtained access and information may disrupt company operations and subvert U.S. research in multiple sectors,” the agencies noted.
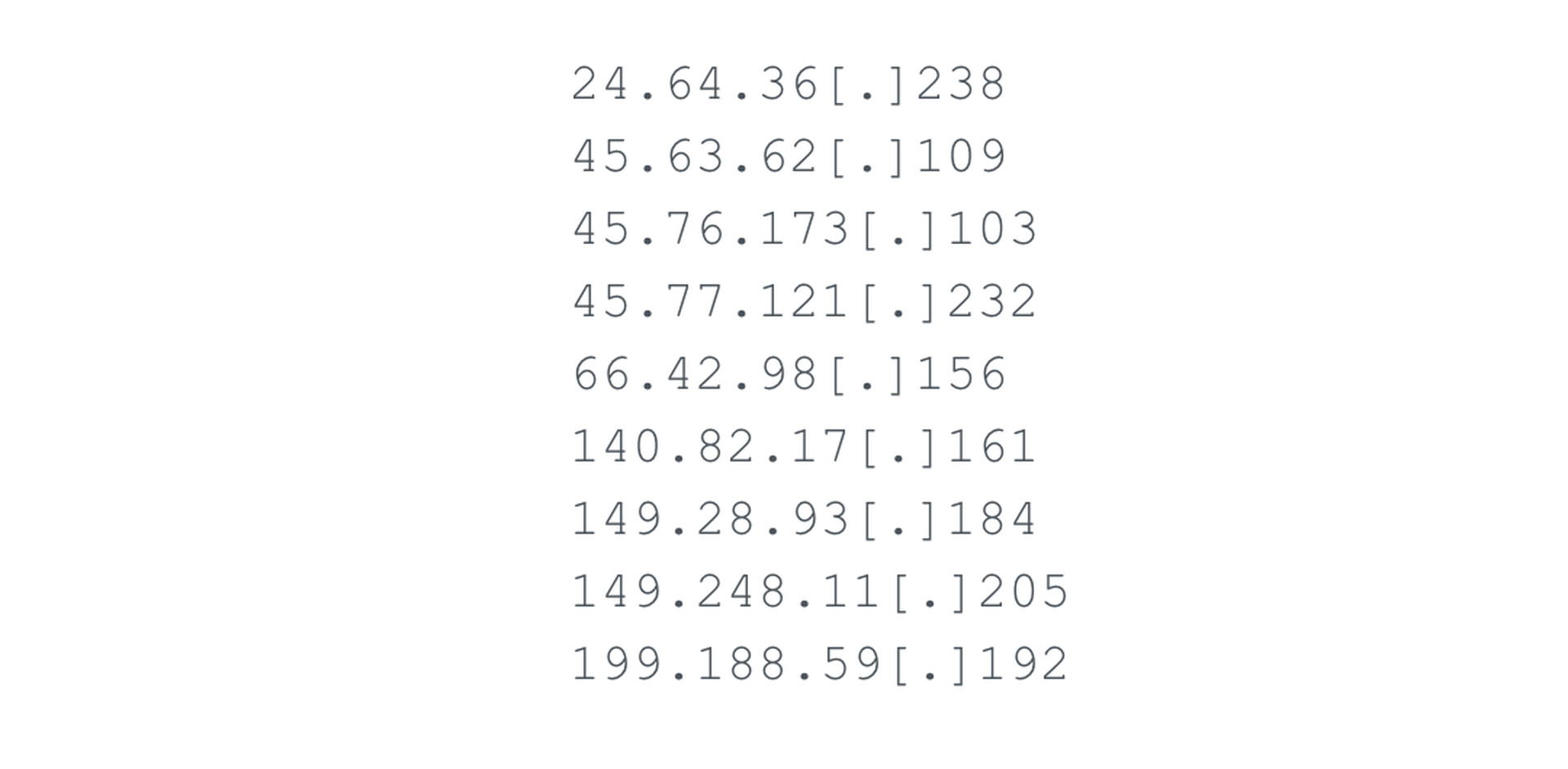
The activity revealed by Palo Alto Networks on Sunday is from a “second, unrelated campaign” targeting the same Zoho vulnerability, the firm said. They too targeted Active Directory shortly after gaining initial access to install credential-stealing malware. In line with previous APT operations, the ultimate objective appeared to be espionage and data theft from a wide range of industries.
“Unit 42 believes that the actor’s primary goal involved gaining persistent access to the network and the gathering and exfiltration of sensitive documents from the compromised organization,” the researchers concluded.
U.S. officials have spent years years ringing the alarm about widespread hacking of U.S. defense contractors by state-sponsored groups, most notably China. The sheer volume of intellectual property theft happening in the defense industrial base – particularly from Chinese-linked groups – has led to a substantial closing of the technological gap between the two nations, according to a 2019 report from the Department of Defense. More recently, Chinese hackers have been increasingly targeting companies that engage in biomedical or biotechnology research as well as a host of other emerging technologies like artificial intelligence and quantum computing, according to the U.S. intelligence community.




