"Technological surprise" is a concept often used by militaries to explain how some technological breakthroughs can happen much earlier than expected, dramatically reshaping battlefield dynamics.
In the scientific and national security worlds, quantum computing — and its malicious cousin, quantum codebreaking — is considered a potentially game-changing technology for modern computing, cybersecurity and encryption. It has also kicked off a race in IT around the world to update the encryption of systems and devices with newer algorithms that can (theoretically) withstand hacks from a future cryptographically relevant quantum computer.
At a Monday event hosted by the Center for Strategic and International Studies, two Biden administrational officials said that while big technological leaps can and do catch policymakers off guard, when it comes to the development of quantum computers that can break modern encryption, the risks are lower because much of the scientific progress relies on a global community of scientists who openly share information with one another.
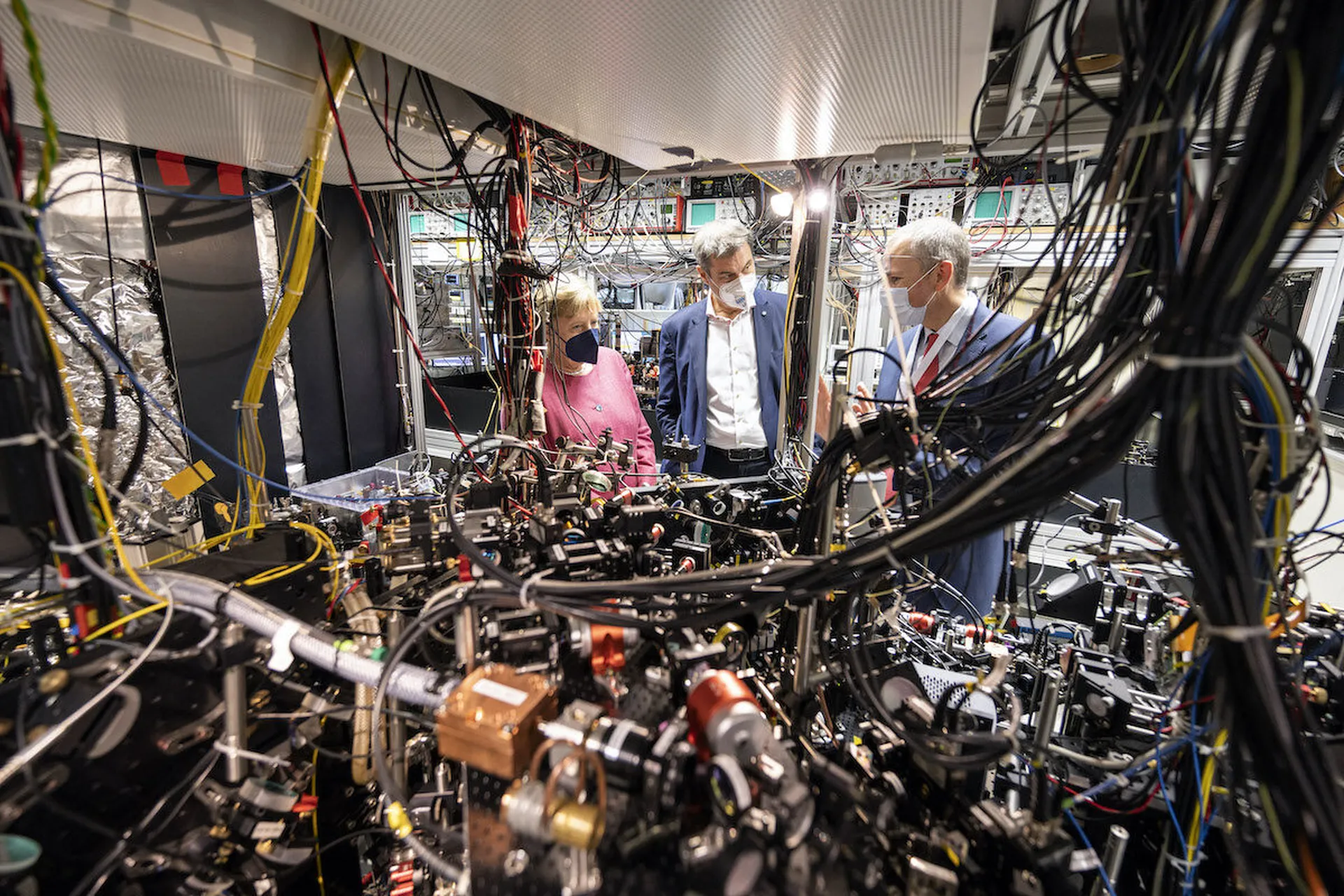
Charles Tahan, assistant director for quantum information science and the director of the National Quantum Coordination Office at the Office of Science and Technology Policy, said there is still so much that scientists don’t know about the applications of a large-scale quantum computer, or even a small-scale one. Solving many of the current obstacles in quantum computing requires constant engagement with a worldwide network of scientists from many different countries.
“The last thing you want to do while you’re discovering new things is close yourself off. You want to work with other people and then pursue the fundamental questions, so that’s No. 1,” said Tahan.
That means there isn’t an easy or straightforward way for any one country to develop those breakthroughs in secret or in isolation without tapping these scientific networks that span borders. While Tahan said he believes the U.S. is ahead of global competitors in the quantum race, he also stressed that America must operate in that same cooperative environment in order to make its gains.
Jonah Force Hill, the director for cybersecurity and emerging technology policy on the White House National Security Council, specifically cited the difference between the scientific approach by the U.S. and countries like China on quantum computing as a distinct advantage.
“I think the United States is in a generally favorable position, vis-á-vie China in this area, because of the collaborative nature of American science and industry … the number of partnerships that this administration has formed with our partners and allies on quantum information science, [research and development], information sharing and academic exchanges,” said Hill. “China, they do not have that same sort of broad coalition working together that we do, so I think it’s a huge competitive advantage.”
The Biden White House recently ordered federal agencies to lay out detailed plans for the looming transition from classical, public-key encryption to more updated algorithms vetted and standardized by the National Institute for Standards and Technology. It’s expected that in the next few weeks, NIST will announce a handful of selected algorithms to officially endorse and enshrine in standards, which will them kick off a series of timelines and mandates for federal agencies to prepare.
A NIST spokesperson told SC Media that the selections are “almost ready” but noted that status hasn’t changed for some time.
The actual replacement of the underlying algorithms and encryption protocols is a job that is expected to take years, but policymakers and quantum scientists have said they believe there is plenty of time. To wit: the current consensus of experts is that a cryptographically relevant quantum computer — a computer capable of processing enough qubits to break through classic public-key encryption algorithms — is still a decade or more away.
Last year, IBM chief technology officer Joysula Rao said IBM’s research on quantum supercomputers indicates that the number of qubits — or quantum bits — required to bust today’s encryption would require processing approximately 6,200 qubits and around 2.7 billion operations. IBM has more recently announced that it hopes to have a quantum computer capable of processing 4,000 qubits by 2025.