The LockBit ransomware group announced on its website it would offer "all security researchers, ethical and unethical hackers on the planet to participate in [its] bug bounty program," with rewards between $1000 and $1 million.
The bounty program was first reported on by VX Underground, is believed to be the first of its kind.
Ransomware groups, like many software-based businesses, run the risk of losing revenue to being hacked — only in their case, it can come by groups assisting victims. In 2021, a the BlackMatter ransom group and its affiliates missed out on "tens of millions of dollars in demands" due to a vulnerability discovered by Emsisoft and shared with other defensive vendors in the industry.
Emsisoft's Brett Callow said this could potentially affect the ability of the industry to repeat that success.
"It could potentially help them identify bugs sooner," he said.
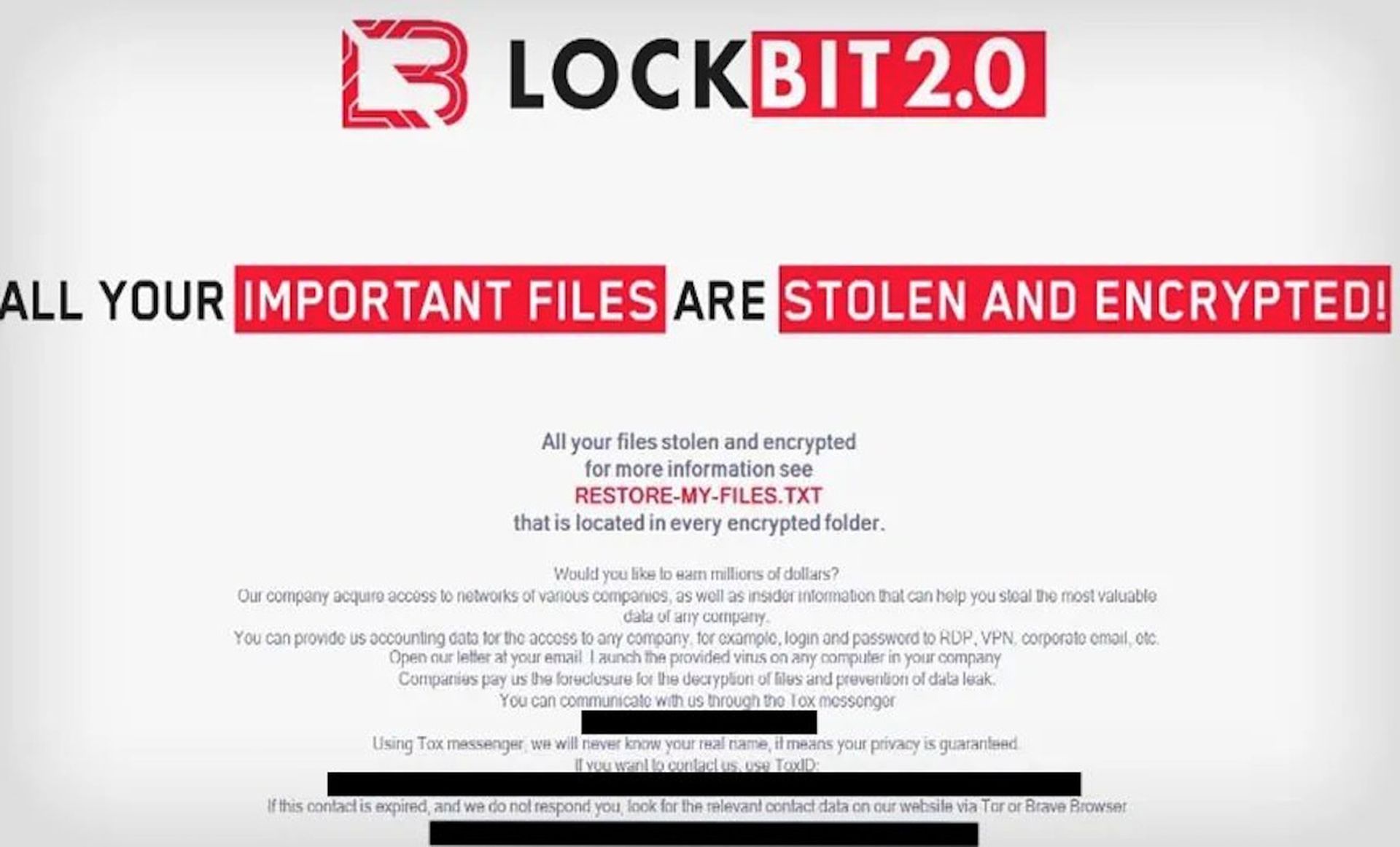
The LockBit ransom program covers bugs on the website, malware and chat program used for negotiations, bugs that reveal the real internet address of the dark web servers used by the group, "brilliant ideas" to boost profits, and doxxing other leaders in the ransomware space. Doxxing has a guaranteed price of $1 million, with bounties not posted for other categories.
The move continues a longstanding pattern of criminal groups using corporate tactics to increase efficiency, including intricate supply chains, industry conferences, call centers and Indeed-level help wanted ads.
None of that should be a huge surprise; successful ransomware groups are more lucrative than most corporations. Over 2021, when LockBit had less market dominance, Chainalysis estimated Conti, the largest group at the time took in nearly $200 million in ransom. LockBit has since supplanted Chainalysis in that top position. The LockBit group and its affiliates may have been responsible for 37.9% of ransomware incidents in the first quarter of 2022, according to Digital Shadows.