LockBit, known for the effective evolution of its tactics, has again modified its variant. In one instance, the ransomware strain was seen targeting Mac devices — the first of its kind for a major ransomware operation.
Patrick Wardle, founder of nonprofit ObjectiveSee, was first to spot a Twitter post from MalwareHunter, which revealed a potential LockBit ransomware sample targeting MacOS. The ransomware binary was initially undetected by traditional anti-virus tools, but has since begun catching the malicious files.
However, Wardle was quick to point out that while the fresh LockBit sample can indeed run on Apple products, “it’s basically the extent of its impact.” As noted, “The codesign utility shows that though it’s signed, it’s signed 'ad-hoc' (say vs. an Apple Developer ID).”
“This means if downloaded to a macOS system, i.e. deployed by the attackers, macOS won’t let it run,” Wardle explained. “This is confirmed by the spctl utility which shows ‘invalid signature.’”
The sample also suggests that it was initially designed to run on Windows. In fact, several sample strings contained nothing that specifically related to MacOS, which may mean the “code is simply a recompile of LockBit ransomware that targets Windows, Linux, and also VMWare ESXi.
So while it’s notable that a LockBit sample has been found targeting MacOS, it’s unlikely the current variant will impact the average user, Wardle stressed. What’s important is to maintain ongoing conversations about detection and prevention of these kinds of threats.
LockBit now borrowing code from Conti
In another fresh campaign, the ransomware appears to rely on the source code of Conti, another highly effective variant. After Conti was disbanded in May 2021, an affiliate leaked the source code of the group that enabled other cybercrime groups to recover the code for future use.
In a sample observed by Glimps researchers, LockBit embedded functions previously used by past interactions of LockBit and Conti family binaries. It was this apparent connection that prompted further analysis and confirmed Conti connections, as well as TrickBot and Bazaloader.
TrickBot was previously employed by the Conti group, which reaffirms the connection. But the BazaLoader tie “is a little more subtle.” Like Lockbit, the group has also been observed using the leaked Conti code.
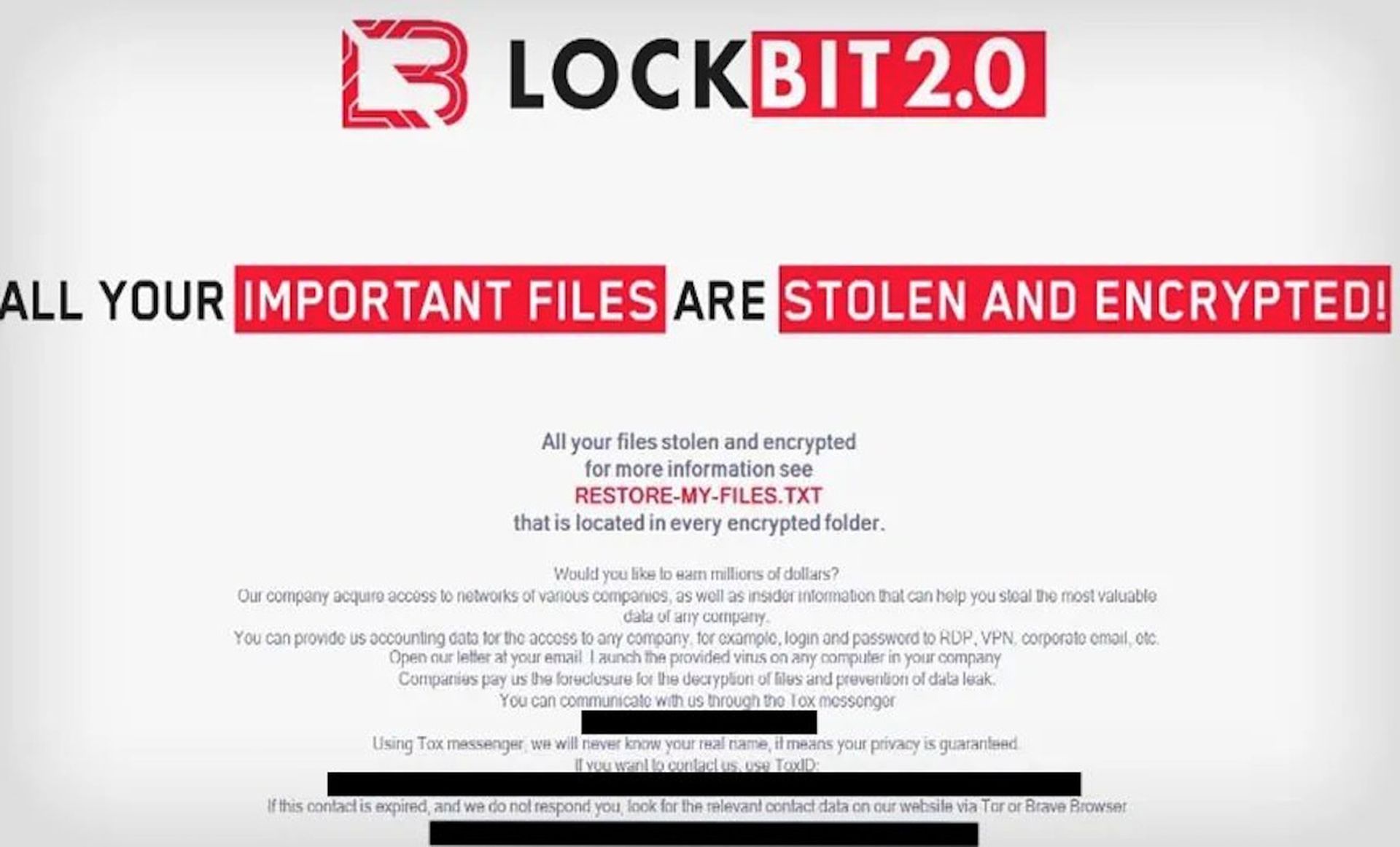
Glimps was also able to examine LockBit’s payment portal and the group’s ransom note, which found evidence of multiple fresh LockBit variants. The ransom note structure bore similarities to previous variants, while the newly detected strains rely on a string of random characters instead of the .lockbit extension.
“The different results produced by the analyzes… confirm what we initially thought: We are indeed faced with variants of Lockbit that shamelessly rely on Conti code, the Lockbit Green version,” researchers wrote.
LockBit is well known for its constant evolution, which has enabled a host of successful attacks across a range of sectors like healthcare. The variant has remained the top attack vector in most ransomware reports since September 2021. A March report confirmed LockBit was behind the Washington state public transit system and ION Group hacks in February.
Most recently, data showed LockBit was leveraging a ransomware-as-a-service (RaaS) model to continue its previous campaigns, which have effectively hindered traditional computer network defenses and mitigation.
Known as LockBit Black, the variant was “more modular and evasive” than previous versions. Much like the Glimps’ findings, LockBit Black shares similarities with Black Matter and Black Cat ransomware.