It’s often said a failure to plan is a plan for failure. Knowing how damaging a wide-scale failure in the nation’s massive financial securities backbone could be, one of the industry’s leading trade associations led a cybersecurity exercise last month to test that readiness.
Last month, more than 900 participants from over 240 financial firms, central banks, regulators, law enforcement and information-sharing groups acted out their response and recovery plans based on a series of simulated ransomware attacks, in a cybersecurity exercise dubbed “Quantum Dawn VI” and led by SIFMA, a securities trade group. SIFMA has been orchestrating these massive cyberattack drills, every two years, going back a decade; the first, Quantum Dawn I, took place in November 2011.
The intent of the exercise was to “assess public and private sector-wide communications and information sharing mechanisms, crisis management protocols, and decision-making, as well as legal and regulatory considerations as exercise participants responded to and recovered from significant ransomware attacks targeting the financial sector,” according to comments from Kenneth E. Bentsen Jr., SIFMA president and CEO, in a prepared release.
“There is likely no greater threat to financial stability than a large-scale cyber incident,” Bentsen said in the release. “Quantum Dawn VI simulated a ransomware event, which underscores this is something the industry must prepare for just as we do for other possible crisis events.”
In the United States alone, capital markets fund more than 70 percent of economic activity, according to SIFMA, and drills like these are vital to ensuring that broker-dealers, asset managers and investment firms are ready when the unexpected occurs. For example, one of the main objectives for this iteration of the Quantum Dawn exercise was incorporating lessons learned from other major cyberattacks and third-party outages, including SolarWinds.
“Financial services continue to be one of the most targeted industries,” said Andrew Howard, CEO for Kudelski Security, adding that his data shows financial was the most targeted industry in 2019 and 2020 and is “on track to top the list again in 2021.”
“Threat actors are looking to leverage their access to financial services organizations to make unauthorized transfers, issue and abuse fraudulent debit cards and gather insider information,” Howard added. “Of course, these organizations are also the targets of ransomware from cyber criminals, but often attackers are able to leverage their access to achieve more long-term goals.” This could include on-going extortion, or causing massive chaotic breakdowns.
Roger Grimes, data-driven defense evangelist for KnowBe4, which runs programs to educate enterprise employees on cybersecurity, said that “no matter how diligent you try to be when planning incident response, there are always things that do not go as previously planned.
Practices like these allow the good, the bad and the ugly to be revealed ... at least as much as it can be done during practice,” he added.
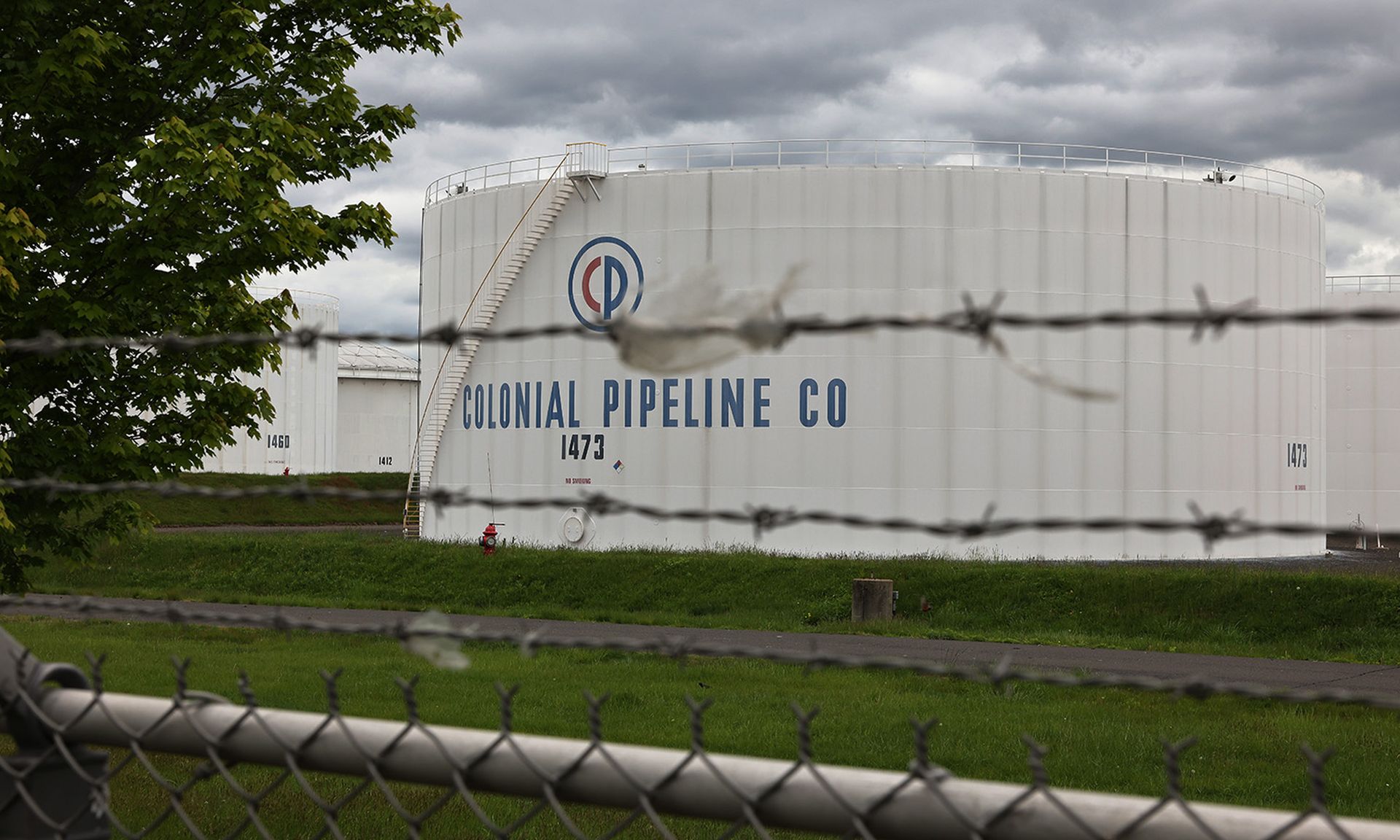
And given the state of high-profile, infrastructure-damaging attacks like we have seen recently with Colonial Pipeline and other companies in other sectors, it seems prudent for the securities industry to be ready for anything— not just the typical cyber-criminal heist.
Increasingly, more rogue nation-states have targeted large financial services and banking organizations, Howard pointed out. In 2016, threat actors in North Korea almost pulled off a $1 billion-plus cyber-robbery from Bangladesh’s National Bank, “which was only thwarted because of a misspelling on SWIFT [wire] transfer instructions that prompted someone in New York to confirm transfer instructions,” Howard said. In the end, the bad actors still got away with $81 million, due to the “significant resources and capabilities” they were able to leverage.
Another potential development that demands more online-oversight: the securities’ industry’s investment in cryptocurrencies. “We’re seeing more of these asset management and investment firms invest in cryptocurrencies and blockchain-based technologies,” Howard continued. "Often these organizations are making purchases and not following best practices to store and hold such assets.” This in turn can permit bad actors to steal cryptocurrency assets “quite easily with little possibility of recovery due to the nature of the assets," he said.
According to Bentsen’s statement from SIFMA, one “clear takeaway from the exercise is the importance of a robust partnership between the industry and government grounded in information sharing. No single actor — not the federal government, nor any individual firm — has the resources to protect markets from cyber threats on their own."