SaaS applications have become commonplace in today’s workforce with tools such as Microsoft Office, Google Docs, Slack, Zoom and many thousands more, even including some lesser known applications, becoming a staple of nearly every work environment. While these products offer tremendous benefits, they also bring additional security risks.
In recent years, state-sponsored threat actors and cybercrime professionals alike have adopted tactics, techniques and procedures for the SaaS domain. Here are three of the most common SaaS attacks:
- OAuth phishing attacks.
OAuth has become a widely used authentication open standard protocol, where users give applications or websites permissions to access their resources on other applications or websites. This does not require users to disclose their credentials. The given permissions vary between applications and might be “read,” “write” or even “manage” permissions, depending on the application’s owner request from the user.
An OAuth cyberattack occurs when a threat actor creates a new malicious application, usually a rogue one, that pretends to be a well-known and used app. In some cases, the threat actor creates the malicious app from a legitimate compromised Office 365 account to appear more trustworthy. It then triggers the victim to grant permissions to the malicious application. If successful, the victim approves the app’s permissions request, and an OAuth token gets issued to the malicious app. It grants the hacker permissions for the victim’s resources, including email accounts, shared files, and contact list.
Cybercrime groups use this technique while targeting businesses around the globe. In July 2020, Microsoft took legal action against an attack that went on for more than six months. The cybercriminals targeted business emails from different sectors in 62 countries, sending phishing emails with OneDrive file links designed to look like they contain business content such as quarterly financial reports. When the victims clicked on the links, they were directed to a web application consent page and were prompted to approve permissions for a rogue Microsoft application created and controlled by the cybercriminals.
- Malicious browsers web-extensions and application add-ins.
Web extensions for browsers and application add-ins are trendy among businesses. These small programs offer a better user experience while using a browser or different applications thanks to personal customization and functionality capabilities. Today, Google Chrome has become the most common browser with almost 63% market share, and there are more than 200,000 Chrome web extensions available to install in the Chrome web store. Unsurprisingly, threat actors use these extensions and add-ins in cyberattacks.
One kind of an attack makes the user install malware that pretends to be a benign extension, but instead the extension or its updates provide the attacker access to sensitive data and organizational resources. In another version of this attack, the extension is benign and does not aim to collect information. However, it may harm the end-point functionality, such as cryptojacking or adware. With the third version, the web extensions are often benign. However, the collected data from the user’s end-point might be mishandled by the extension’s owner. For example, the owner can sell the collected data to a fourth party.
By the end of 2020, it was found that more than 3 million users worldwide installed 28 malicious web extensions of Google Chrome and Microsoft Edge. Some of them were active at least from 2018, according to Avast. The main goal of these malicious extensions was to redirect users to third-party domains - phishing sites and ads - and hijack their traffic for financial profits. It’s unknown whether it was the extensions or their updates that were malicious.
- Brute-force attacks.
Threat actors try to compromise valid accounts in Single Sign-On (SSO), federated services and cloud applications. Compromising a valid account in such applications bears the opportunity to access a handful of resources and sensitive data at once. It’s possible because of the interconnectivity between SaaS apps. Microsoft stated it detected more than 25.6 billion attempts to hijack its enterprise customer accounts of Azure Active Directory by brute-forcing stolen passwords in 2021 alone.
In these kinds of attacks, the actor tries to sign-in to accounts multiple times with a set of passwords. Phishing attacks are also another common way to steal valid passwords, and they are quite effective. Organizations that do not implement or do not enforce robust authentication methods, such as MFA, are far more exposed to these attacks. And yet, Microsoft indicates that only 22% of users and 30% of global admins use MFA among their Azure Active Directory customers.
The Russian state-sponsored actor campaign that was discovered last February was actively collecting sensitive information from networks of multiple cleared defense contractors (such as vehicle and aircraft design, weapon and missile development and even data analytics) in the United States, during a period of almost two years. Their goal: obtain sensitive national defense information and technology.
The Russian state-sponsored actors who were behind this campaign used compromised Office 365 service accounts, including accounts with global administrator privileges, to collect data from Office 365 resources such as emails, profiles, and SharePoint.
The attack vectors we covered here are examples of common tactics, techniques and procedures that use SaaS as their attack surface. It’s important to note that these are not the only attack vectors that take advantage of SaaS applications. They are all part of a rapidly growing attack surface introduced by SaaS.
These attack vectors emphasize the need for understanding and controlling businesses' SaaS estate. This includes all the SaaS applications their employees use for work, both approved and unapproved. Once a company maps out the magnitude of its SaaS usage, it’s critical they put in a remediation plan to solidify their security posture.
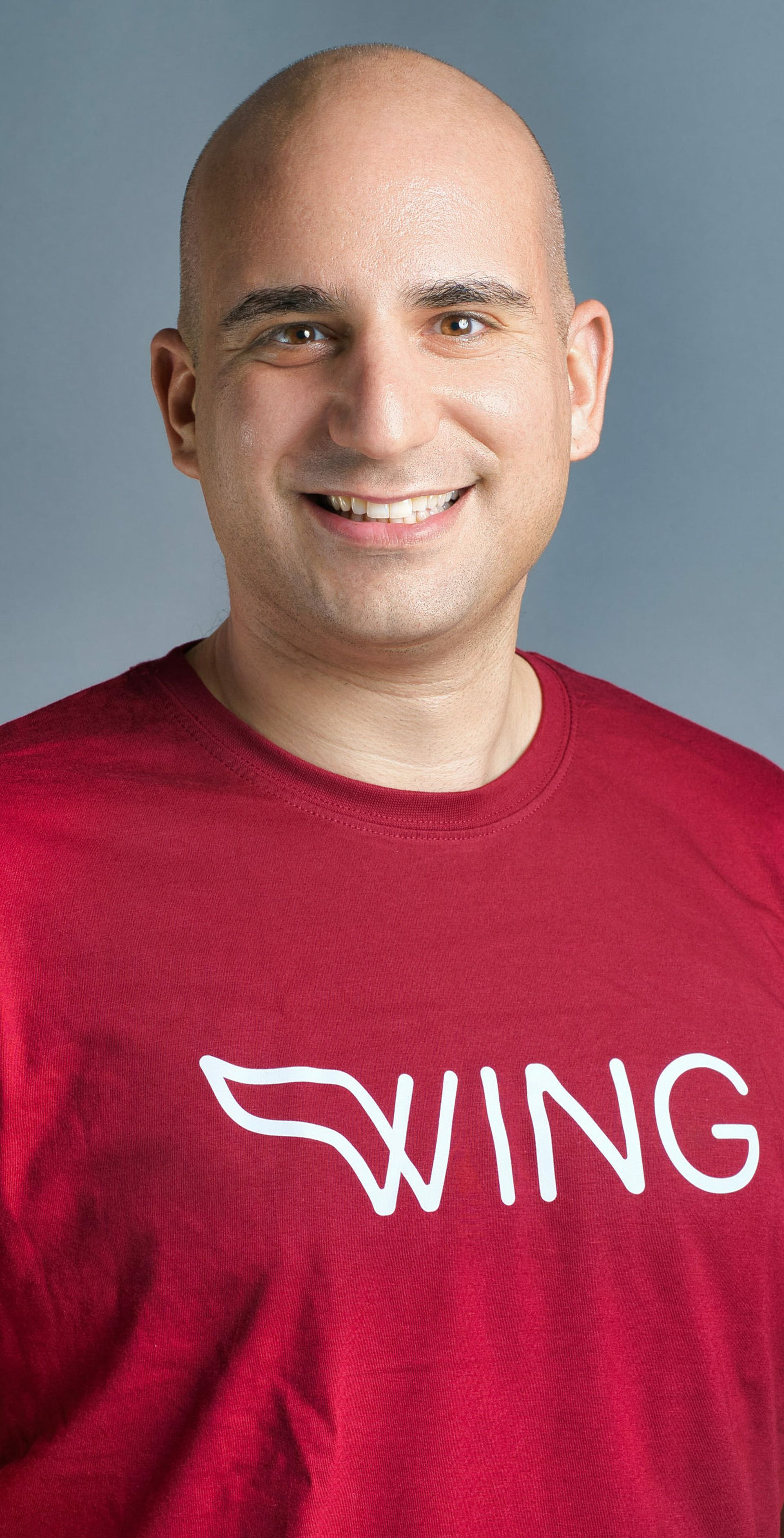
Yoav Kalati, head of threat intelligence, Wing Security